Enforcement
Enforcement is the process during which HelloID Provisioning performs Grant, Revoke, Update and Unmanage actions on Entitlements in target systems. Missing entitlements are added and unauthorized ones are removed, so that persons have exactly the access they should have in target systems, as determined during the Evaluation.
Every organization's user accounts go through a "CRUD" lifecycle: Create, Enable, Update, Disable, Delete. These stages correspond to an employee's status in the organization, from onboarding, to role changes, to promotions, to eventual offboarding. In HelloID, the entitlements associated with this lifecycle are controlled by Entitlement actions.
To get started, manually Run an enforcement, or Add a schedule with enforcement enabled.
Important
For an enforcement to do anything at all, at least one of the following must be true:
Something in a source system's configuration (source mappings, display name formatting, primary contract & manager determinants) has changed since the last enforcement, and a new Source snapshot has been generated.
One or more Business rules have been modified since the last enforcement.
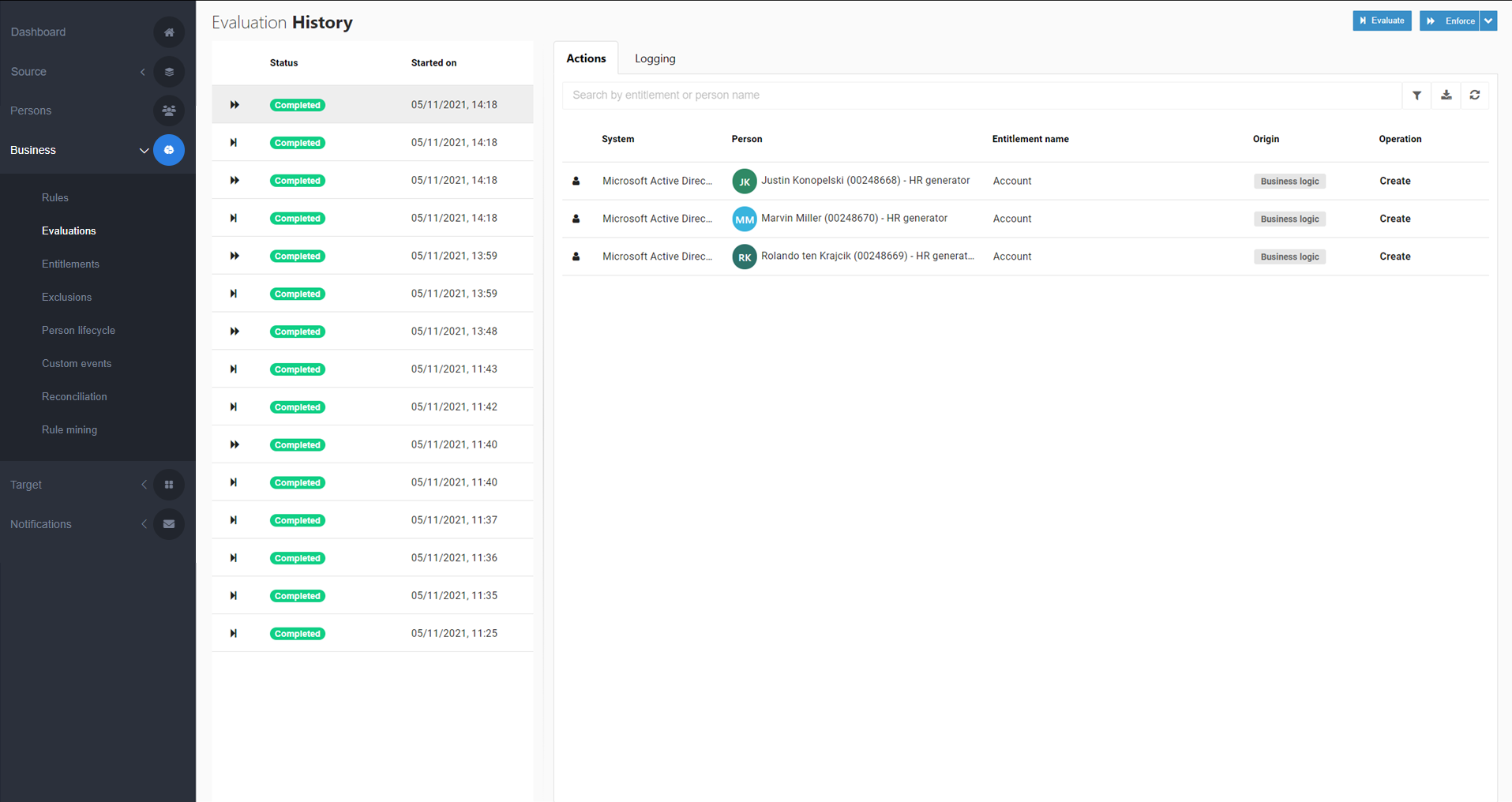
If neither of these are true, running an enforcement does nothing. To preview the actions that will occur during the next enforcement, see Evaluation.
Related features include:
Update accounts: writes certain changes into Target systems which are not normally included in an enforcement.
Retry failed action: retries a single entitlement action that failed during an enforcement, without performing another full enforcement.
Re-enforce an entitlement: re-enforces only a single granted entitlement, without performing a full enforcement.
Run with resources: runs a standard enforcement (Run an enforcement), but additionally processes Resources just prior to the enforcement. If resources fail, there is no stop condition. The enforcement continues and all entitlement actions are still attempted. However, any entitlements which depend on failed resources will also fail.