Amazon AWS AppStream SAML application setup
Introduction
Amazon AWS Appstream allows you to stream desktop applications to your end user's devices. This provides a consistent and convenient application experience for your end users, regardless of their hardware capabilities.
This article will guide you through creating a SAML authentication configuration between HelloID and your Amazon AWS Appstream instance.
Requirements:
HelloID environment
Amazon AWS Subscription
Create or Import a Certificate
If there is no certificate yet, a certificate must be imported or created. This can be done in the HelloID Administrator Portal under Settings > Certificates. For this tutorial, we will use a self-signed certificate. Learn more about certificates here.
Application Setup
Add the AWS AppStream Application
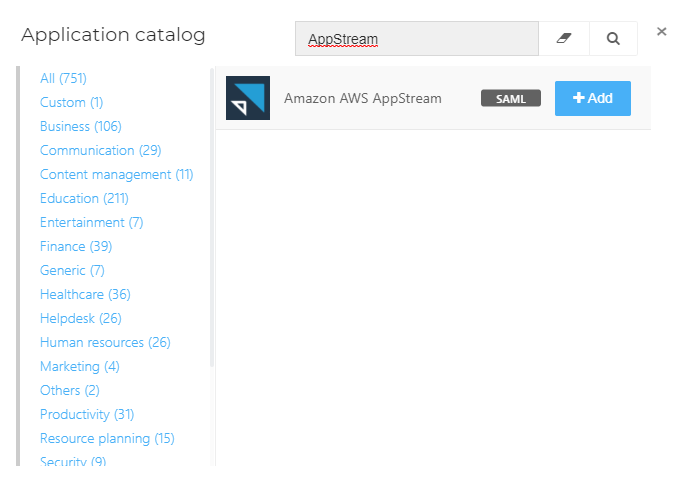
Create a new application in HelloID by navigating to Applications > Applications. Open the Application Catalog and search for "AppStream". Find the SAML template, and click Add. Learn more about managing applications here.
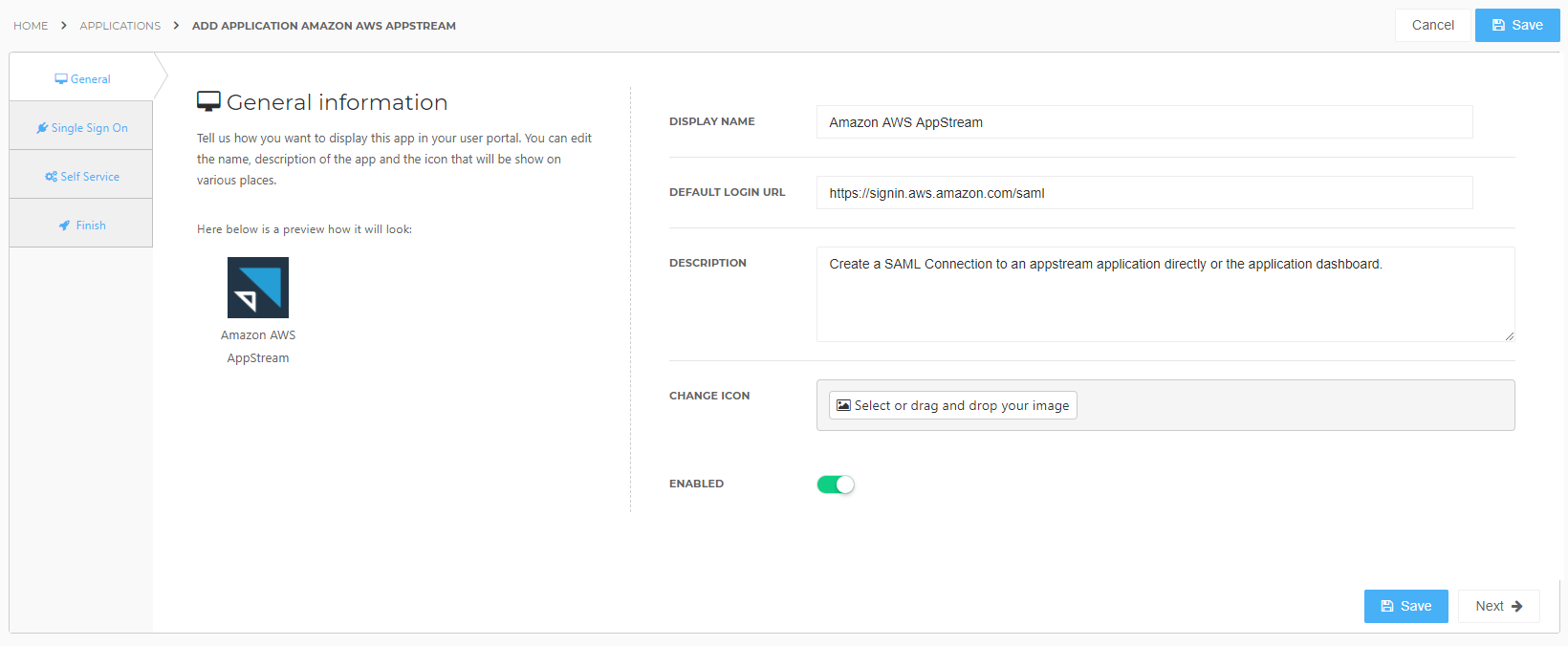
General Tab
On the General tab, you may change the display name and description of the application. When you are finished, click Next.
Single Sign On Tab
On the Single Sign On tab, make the following changes and click Next.
In RelayState URL, replace the {Region}, {StackName}, and {AWS Account Id} variables with the relevant values from your AWS instance.
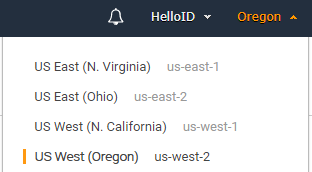
Region will be the server associated with your chosen AWS region. In the screenshot below, it would be us-west-2.
StackName will be the name of the AppStream stack you wish to connect to.
AccountID is your unique AWS account ID, found by going to My Account in the top navigation bar of your AWS management console.
Optional: You can configure this connection to automatically launch a specific application by appending the application's name per this AppStream Relay State documentation. Doing so will limit this HelloID application to launching just that one AppStream application, but it can provide a more convenient user experience.
In the X509 Certificate dropdown, select the certificate that you created or imported previously.
Click Next.
Self Service Tab
On the Self Service tab, choose whether to automatically create a Self Service product, which makes the application requestable. This is optional. Click Next.
Finish Tab
On the Finish tab, click Save to add the application to HelloID.
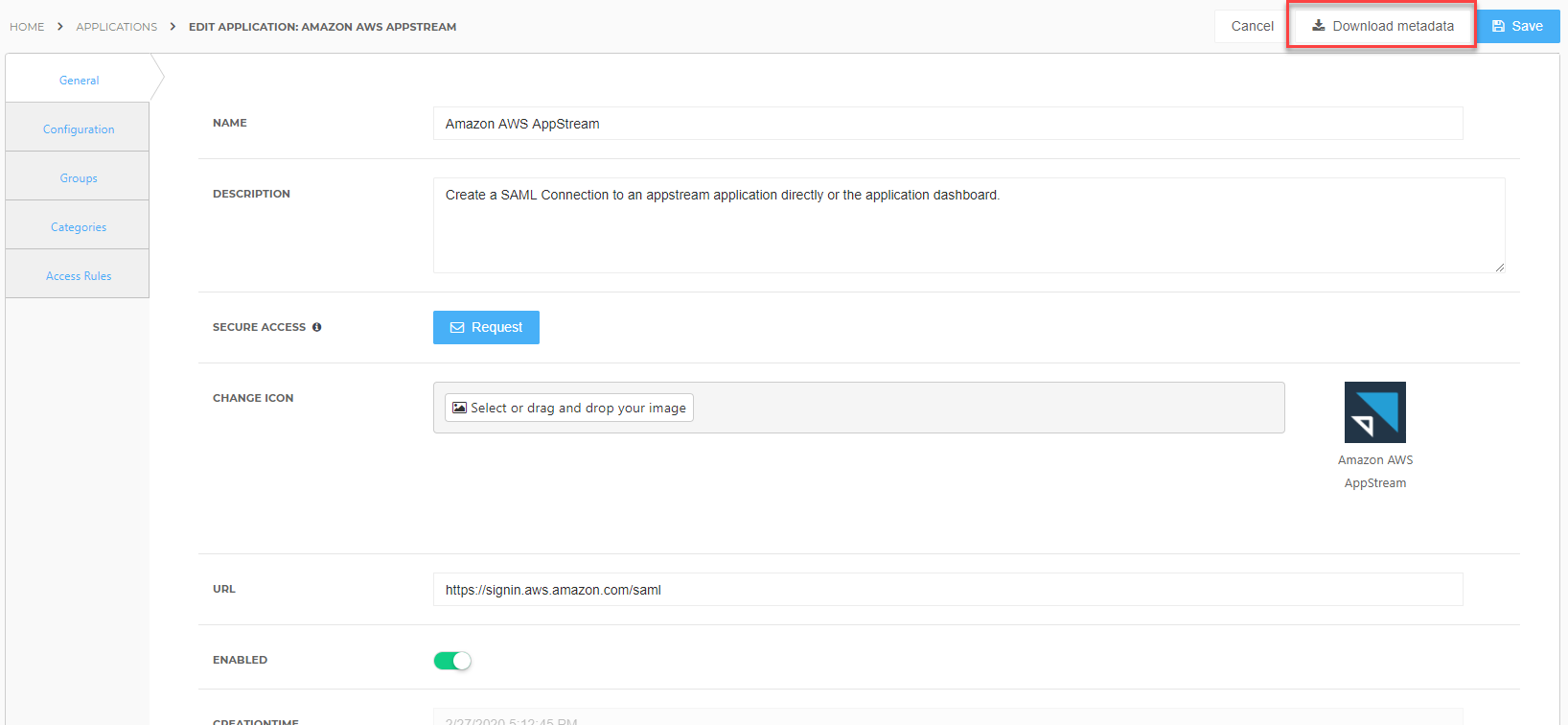
Application metadata
After saving the AWS AppStream application, click its Edit link on the applications overview. This will bring you to its properties page. Click the Download metadata button to download the application's metadata XML file. You will need to provide this to Amazon AWS in future steps.
Configure Amazon AWS
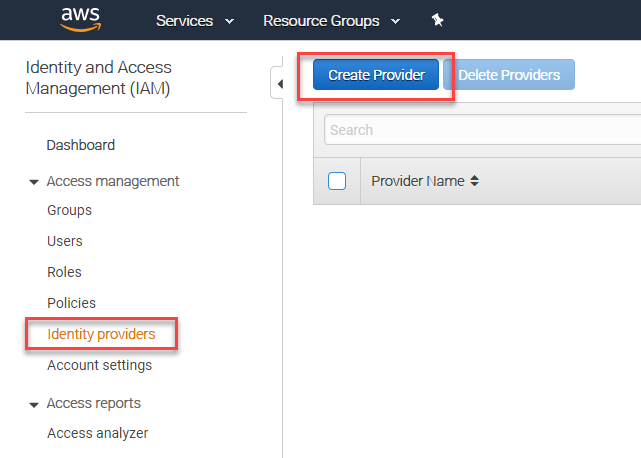
Create an Identity Provider in AWS
Log in to your AWS Management Console and open the IAM console.
On the navigation menu, select Identity Providers. Then, click the Create Provider button.
Make the following changes on the next page and then click Next Step.
Provider Type: Select SAML from the dropdown menu
Provider Name: Provide a name such as "HelloID", or a more specific name if you chose to target the connection at a specific application.
Metadata Document: Upload the metadata.xml file that you saved in previous steps.
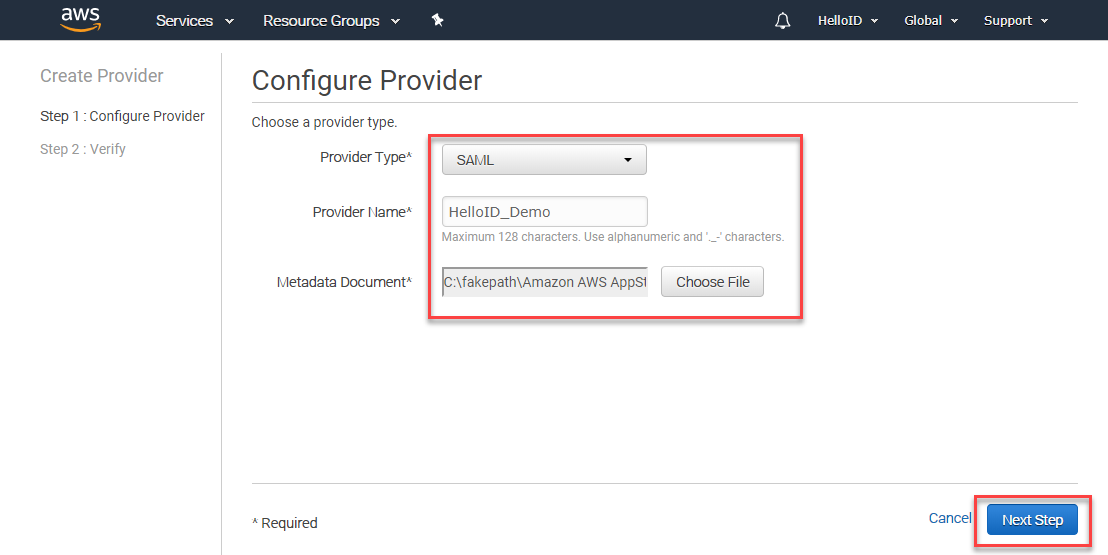
Click Create on the next screen.
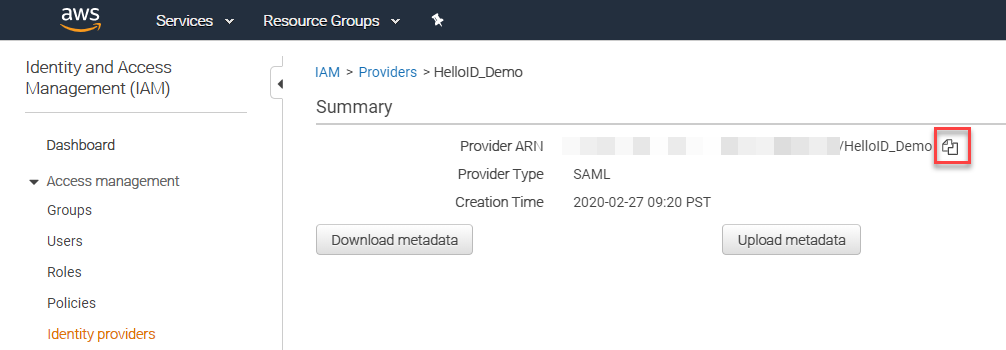
Click on the name of the newly created Identity provider record to view its properties.
Click on the copy icon next to the Provider ARN value. Make note of this value somewhere, as you will need it in later steps.
Create a SAML Role
In the AWS IAM console, select Roles in the navigation bar.
Click the Create role button.

Select SAML 2.0 federation and then make the following changes:
SAML provider: Select the identity provider that you created in previous steps.
Do not select either of the radio buttons below this dropdown ("Allow programmatic access only" and "Allow programmatic and AWS Management Console access").
Attribute: Select SAML:sub_type
Value: Type persistent
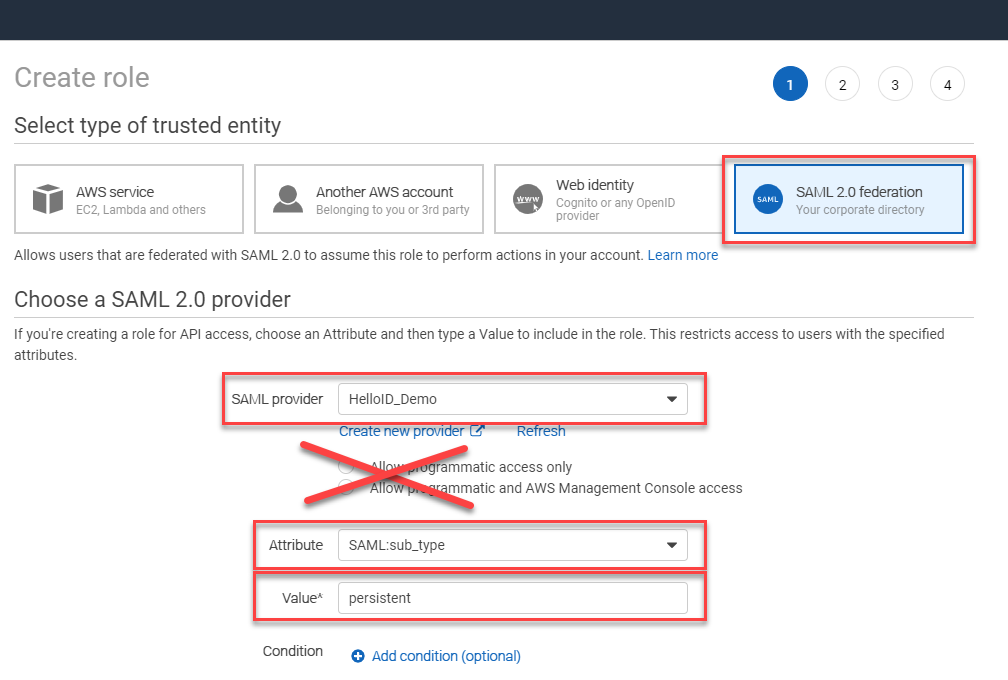
Click Next: Permissions
On the Attach permissions policies page, you will need to apply an inline policy to this role. The specifics of the policy will vary from organization to organization, and are outside of the scope of this article. Refer to the AppStream SAML documentation for more information. When you are finished, click Next: Tags.
On the Add tags (optional) page, you may add any tags that you deem necessary for this role. You can learn more about tags here. Click Next: Review when you are finished.
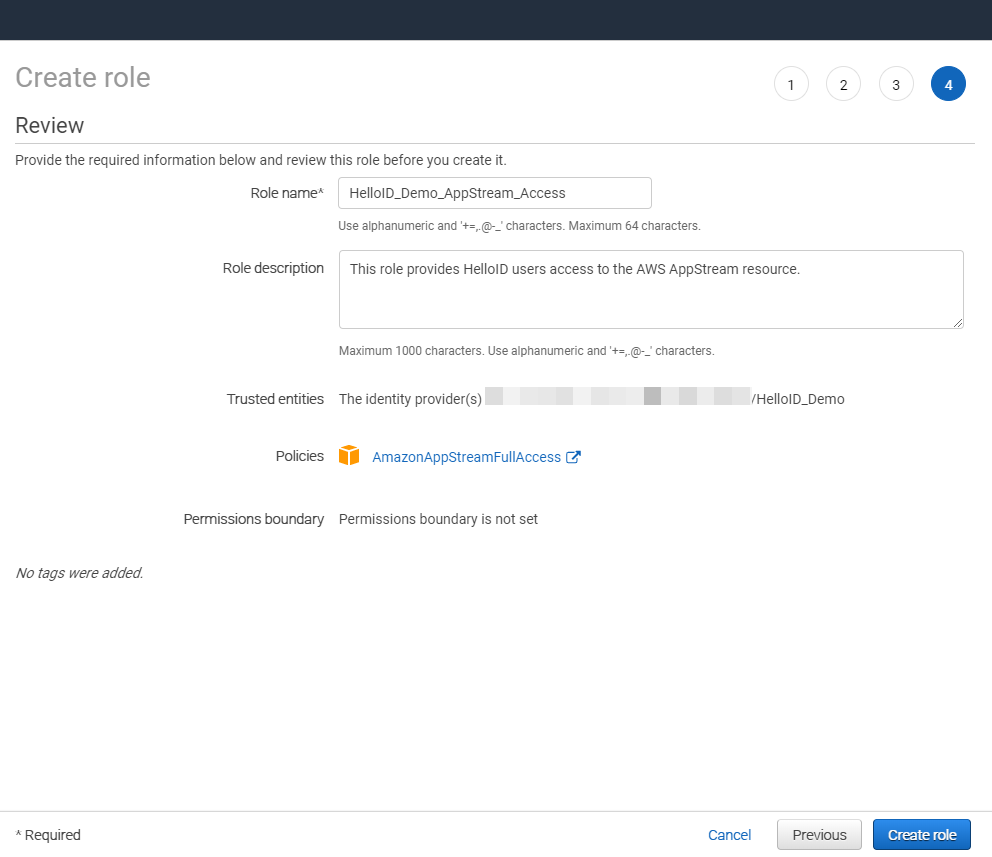
On the Review page, provide a name and an optional description for your new role. Note that the name cannot be changed later. Click Create role when you are finished.
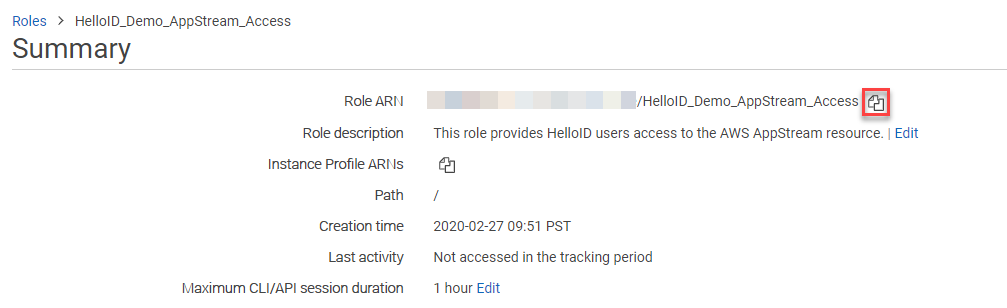
Click on the name of the newly created role to access its properties. On the Summary page, click the copy icon next to the Role ARN value. Make note of this value, as you will need it in later steps.
Configure AppStream Mapping in HelloID
Now that the connection from AWS AppStream to HelloID has been configured, it's time to return to HelloID and update the application's configuration. You will be providing it with the Provider ARN and Role ARN values that you copied in previous steps.
In the HelloID Admin Console, navigate to Applications > Applications.
Search for or find the AppStream application you added earlier and click its Edit link.
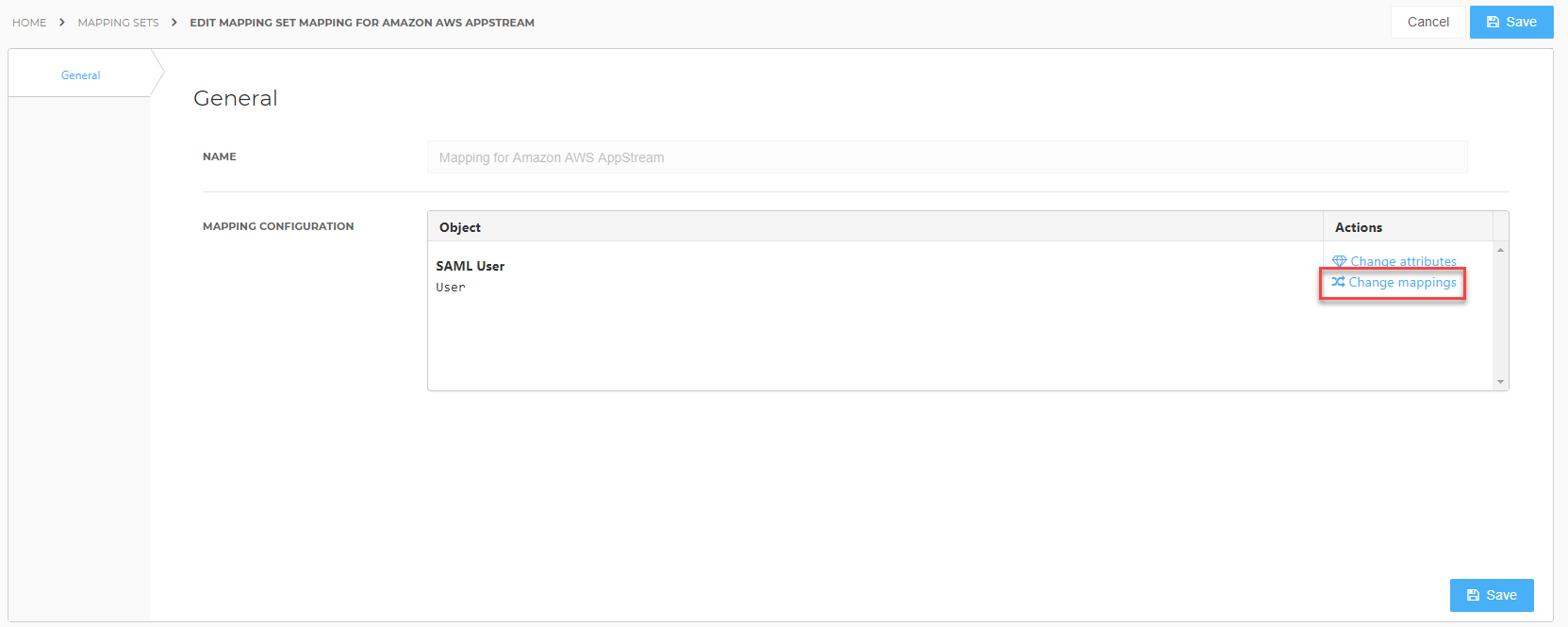
Navigate to the Configuration tab. Scroll down and click on the Configure Mapping Set button. When prompted to continue, click Proceed.
Click the Change mappings link.
Replace {Role ARN} and {Provider ARM} with the Role ARN and Provider ARN values that you copied earlier. Be sure that the comma remains between them and there are no extra spaces anywhere.
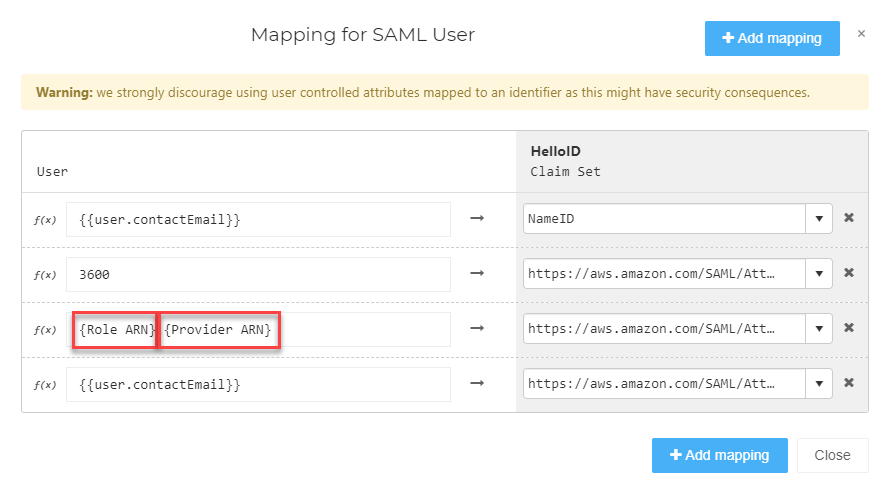
Click Close and then click Save.
Finishing Up
The Amazon AWS AppStream application has now been added to HelloID, and a trust has been configured between AWS and HelloID. You are now free to assign the application to users within your organization and begin testing it and using it. You can learn more about managing applications and assigning permissions here.