MyWorkDrive application setup
Introduction
This article demonstrates how to set up HelloID and MyWorkDrive for single sign-on using the SAML protocol. The configuration takes place in HelloID and MyWorkDrive.
Requirements
HelloID environment
MyWorkDrive environment
Create or import a certificate
If there is no certificate yet, a certificate must be imported or created. For this tutorial, we will use a self-signed certificate. Create one before proceeding and name it MyWorkDriveSelfSigned.
Application setup
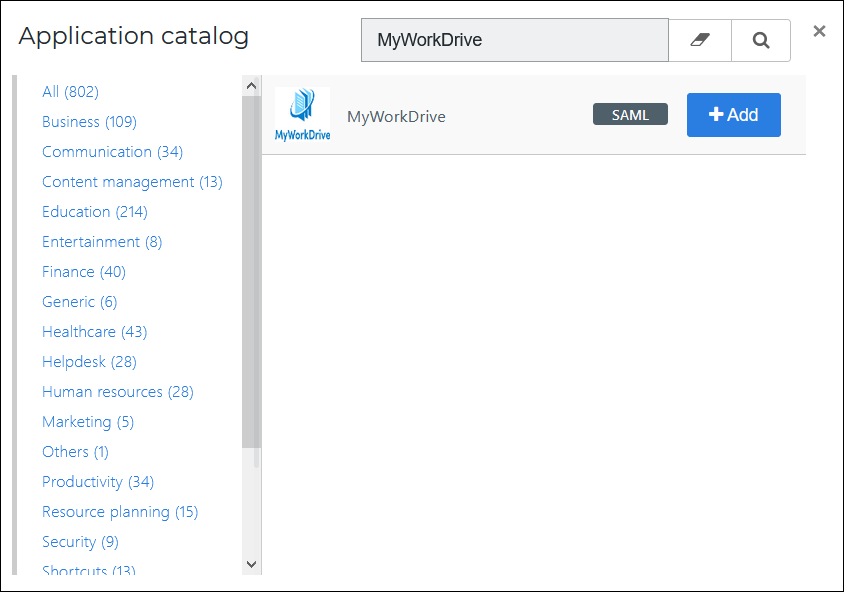
Add the MyWorkDrive application
Go to Applications > Applications and select the Open application catalog button. Find the template for MyWorkDrive and select its Add button. Learn more about managing applications here.
General tab
On the General tab, the default settings can be accepted.
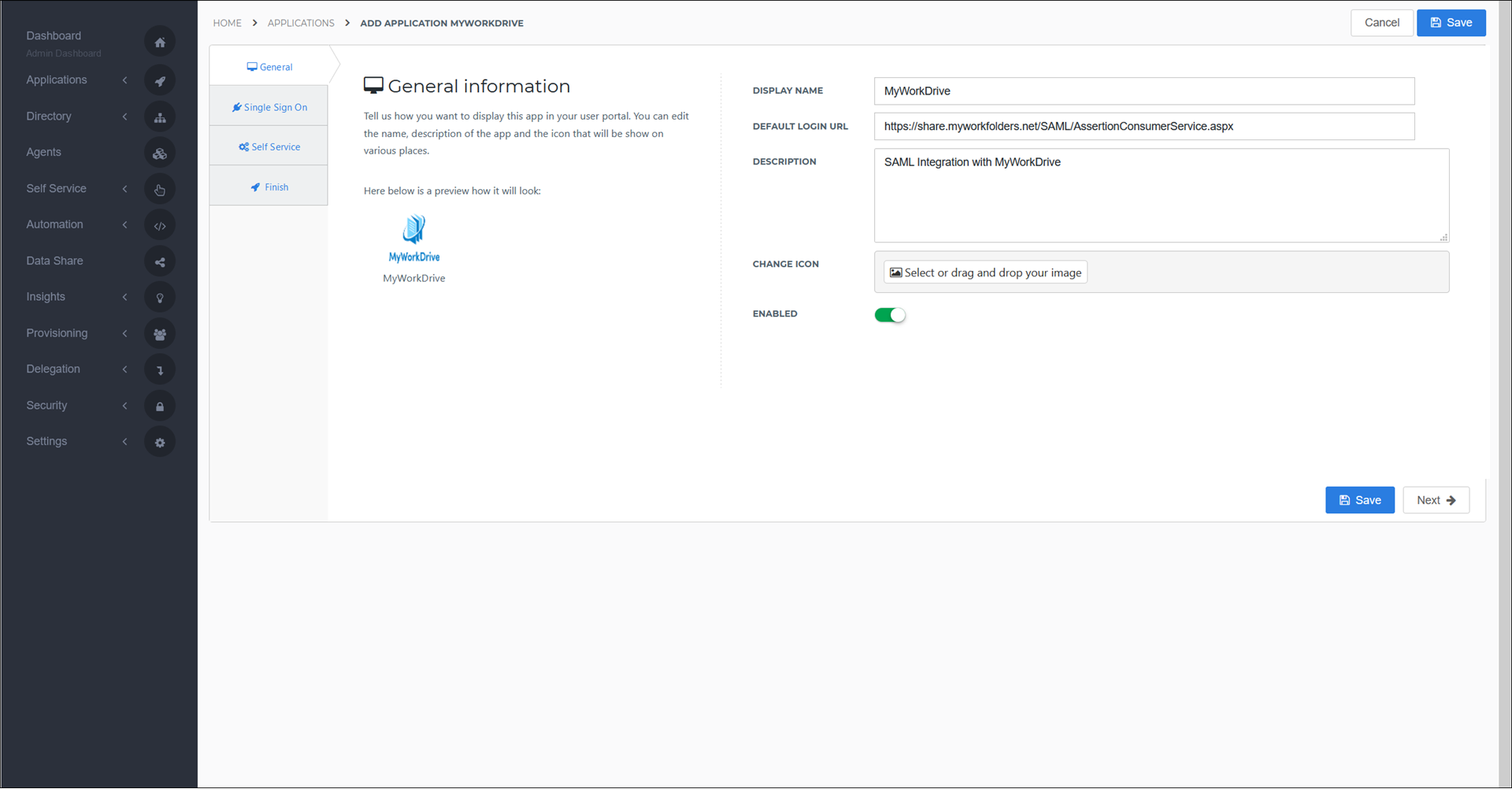
Select the Next button.
Single Sign-on tab
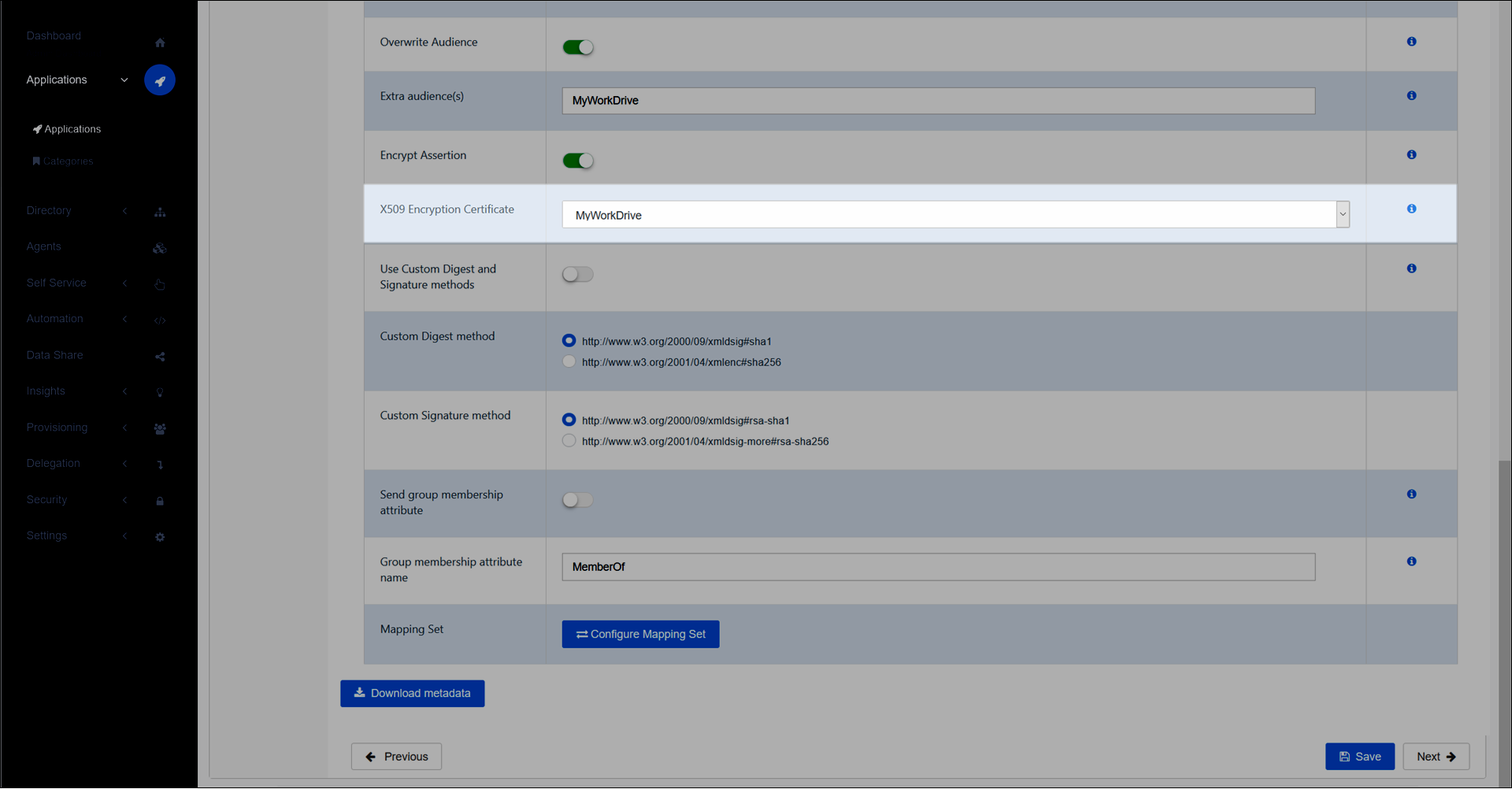
On the Single Sign-On tab, select your previously-created MyWorkDriveSelfSigned certificate for the X509 Certificate drop down. All other settings can be left as default.
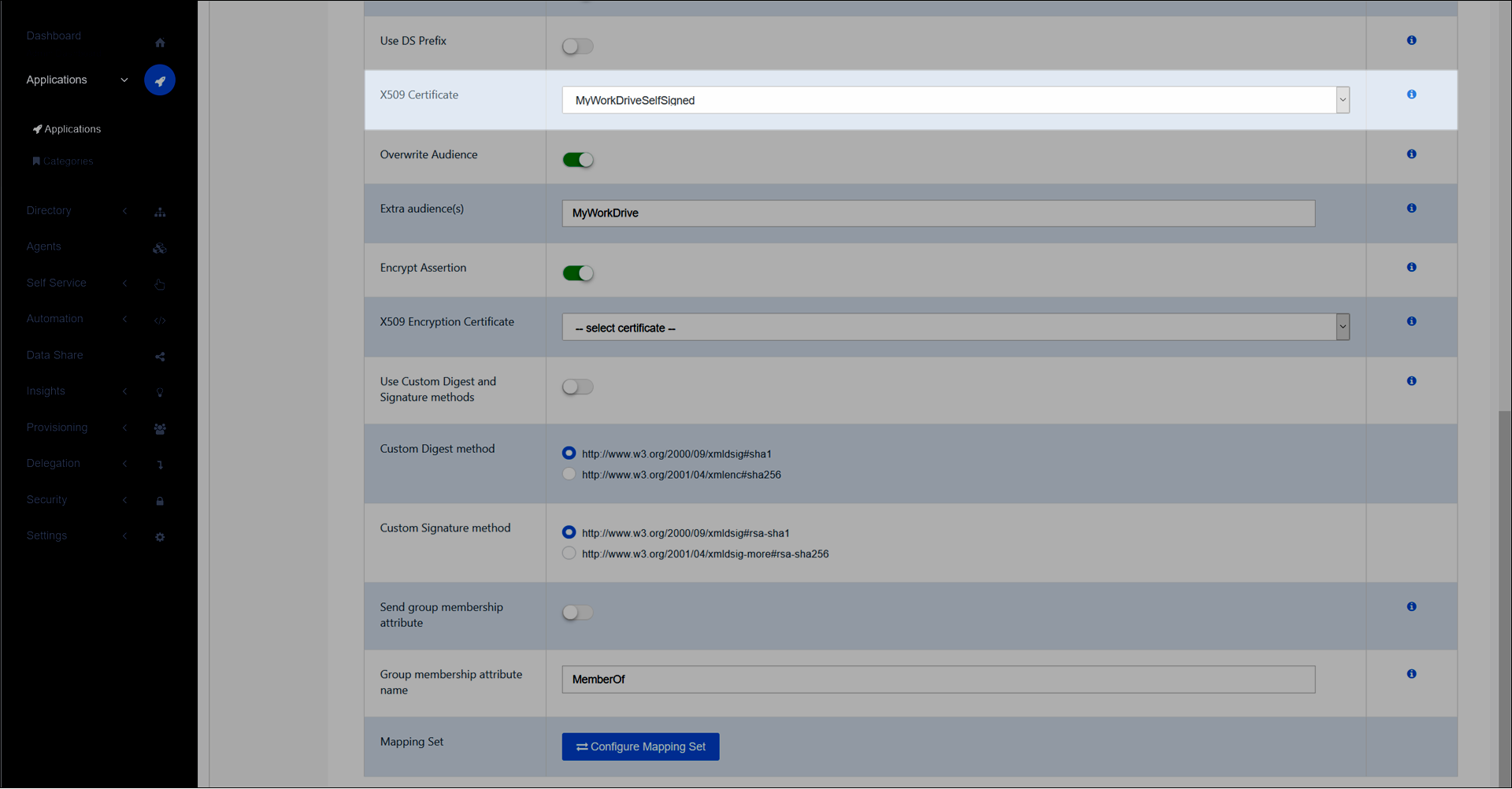
Select the Next button.
Self service tab
On the Self Service tab, choose whether to automatically create a Self Service product, which makes the application requestable. Select a group which will have access to the product. This is optional.
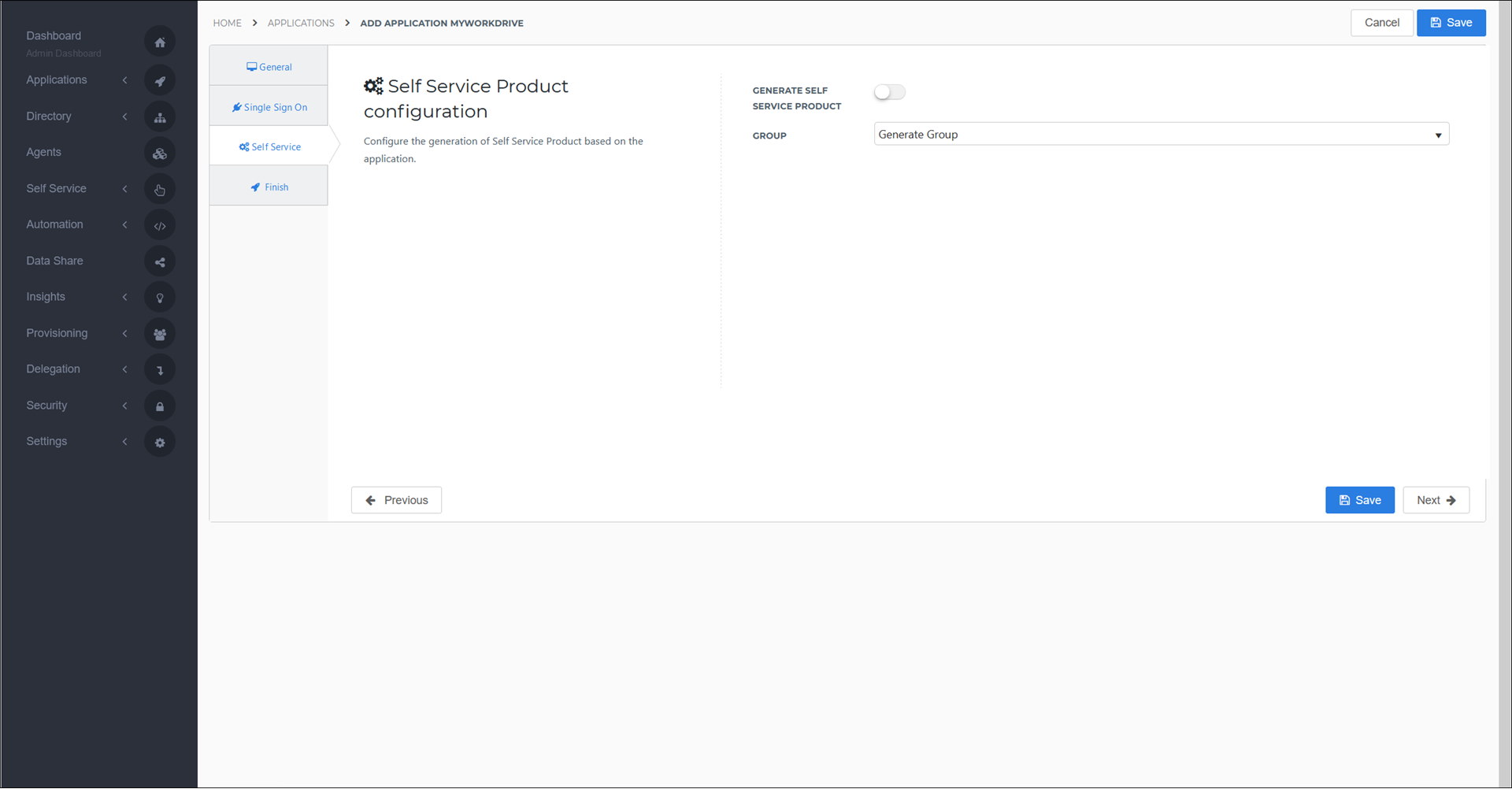
Select the Next button.
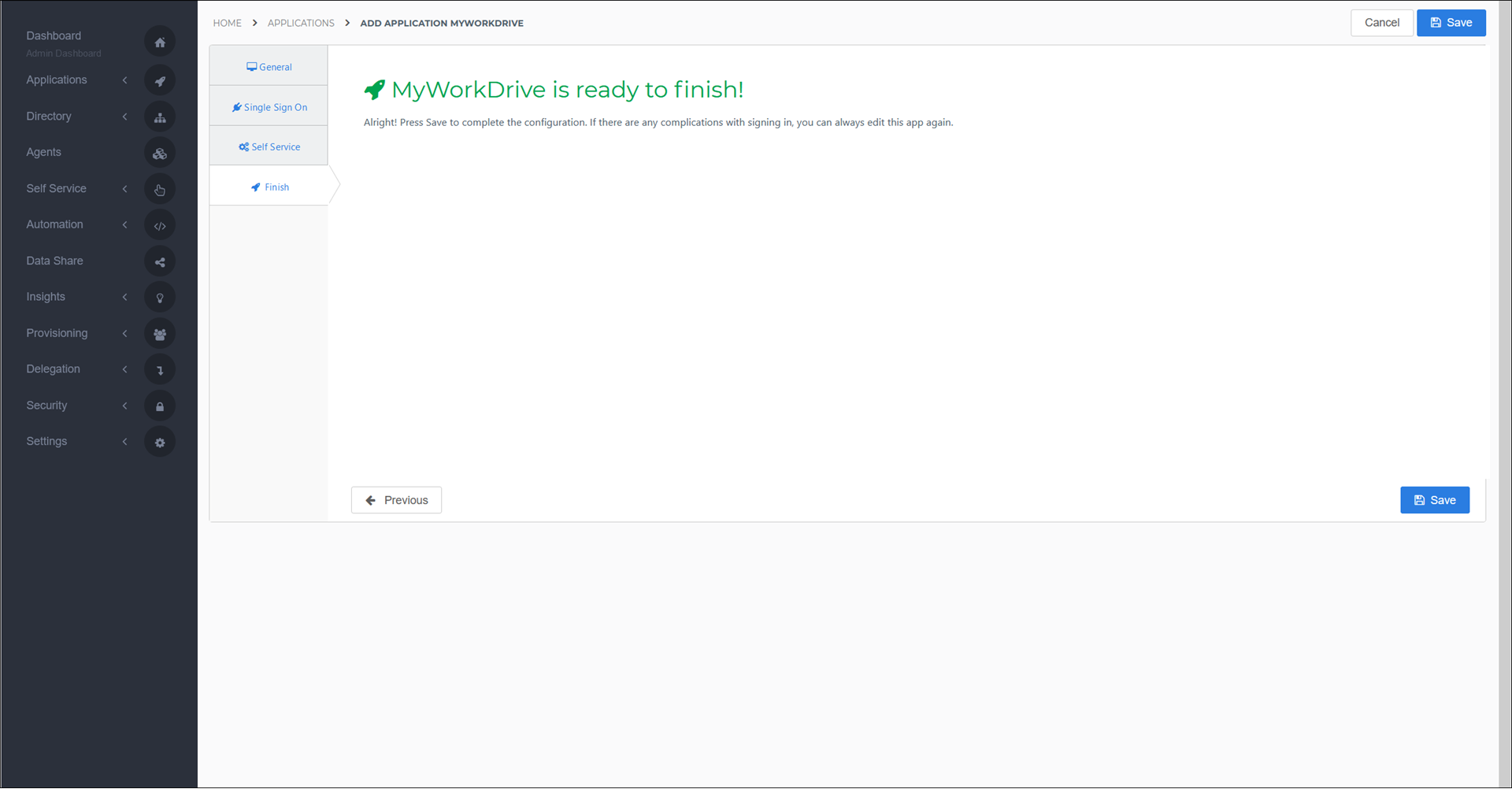
Finish tab
On the Finish tab, select the Save button to add the MyWorkDrive application to HelloID.
Configure the mapping set
By default, the user's HelloID {{user.contactEmail}} attribute is sent as the SAML NameID. If you wish to use another attribute, see Mapping - Overview.
Supplier-side configuration
The HelloID side of the configuration is now finished. You must now enter the dynamic metadata URL on the MyWorkDrive side.
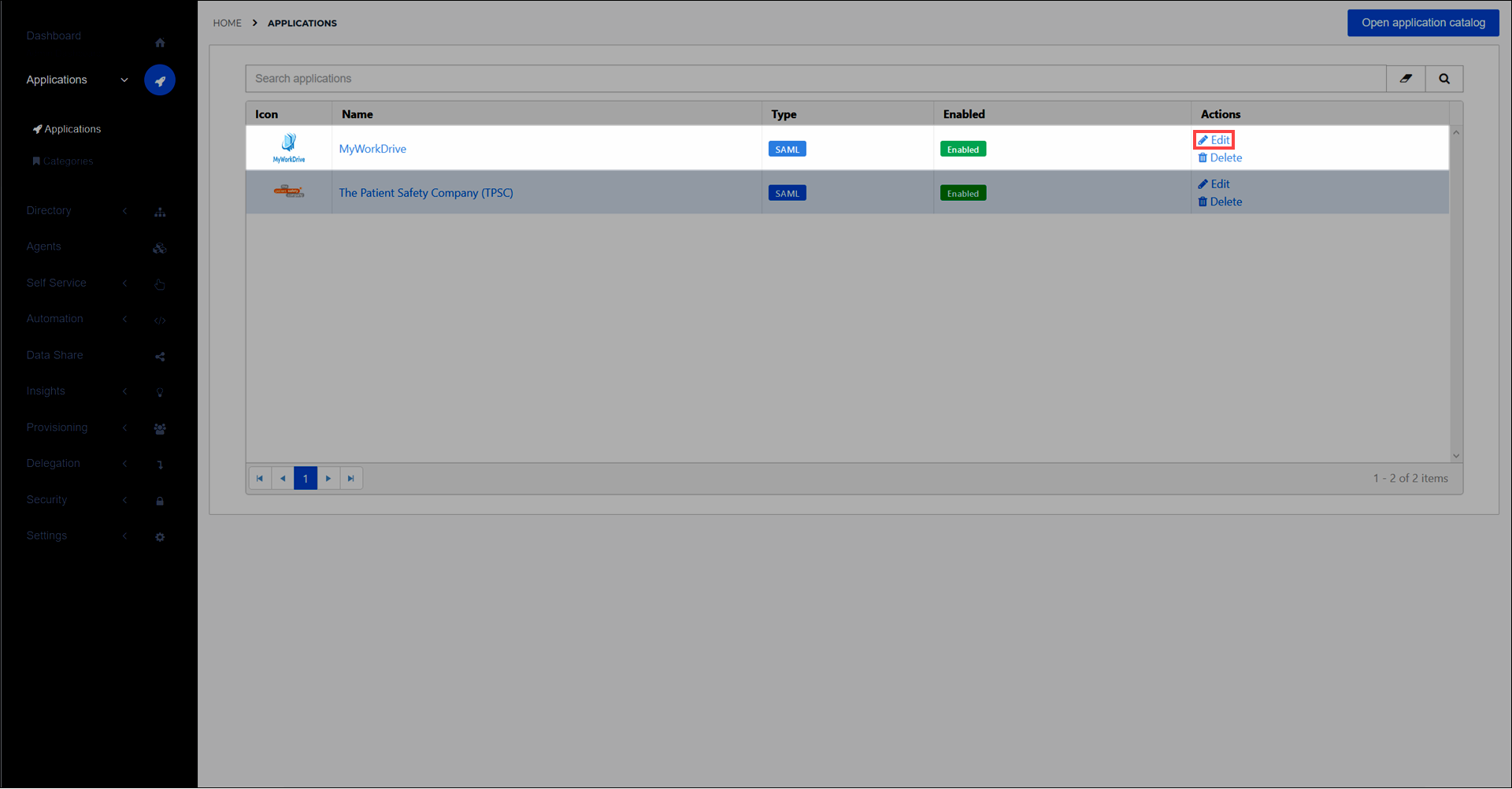
Go to Applications > Applications and select the Edit link for the newly-added MyWorkDrive app.
Right-click the Download metadata button and select Copy link address. It will resemble something like
https://enyoi.helloid.com/metadata/download?ApplicationGUID=e6e741f5-a469-4849-93f7-fe2e259a339f.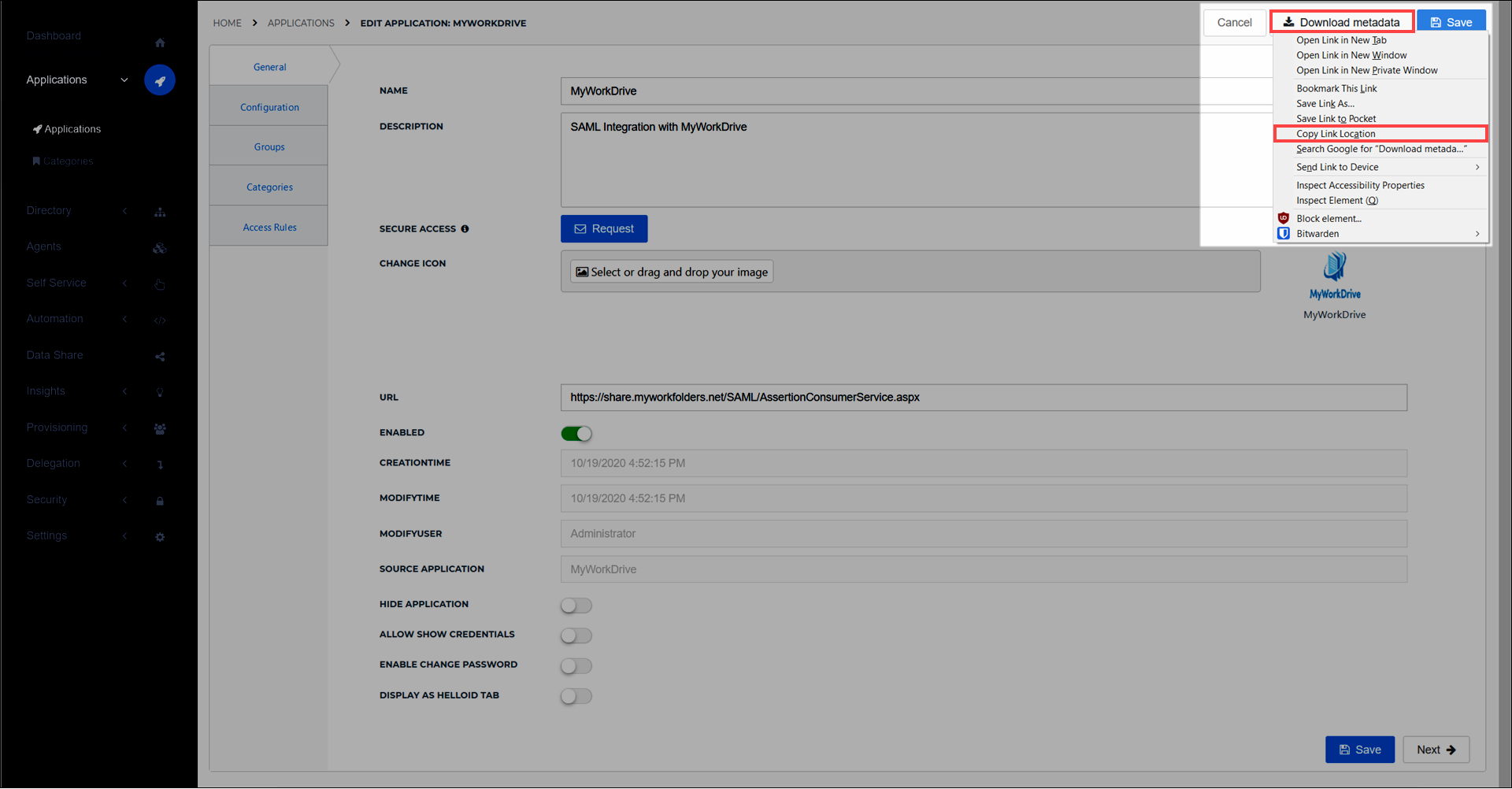
Go to the MyWorkDrive Enterprise settings page.
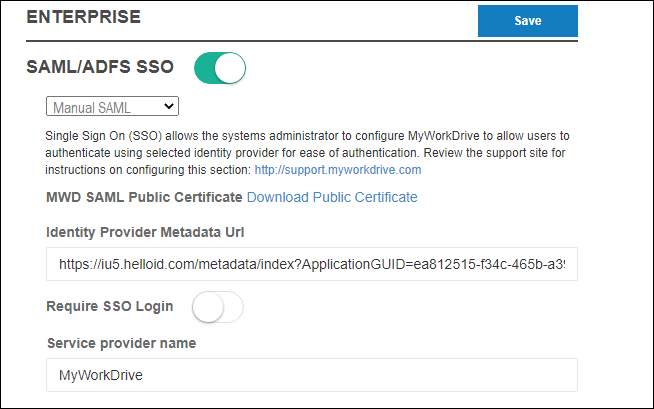
Turn on the SAML/ADFS SSO toggle.
Select Manual SAML from the drop down.
Paste the dynamic metadata URL into the Identity Provider Metadata URL field.
Enter
MyWorkDrivein the Service provider name field, if it is not already entered.Select the Download Public Certificate link and save the file to your hard drive.
Select the Save button. Setup is now complete, and your
saml.configfile has been updated. It will now look like this:
<?xml version="1.0" encoding="utf-8"?> <SAMLConfiguration xmlns="urn:componentspace:SAML:2.0:configuration"> <PartnerServiceProviders> <PartnerServiceProvider Name="MyWorkDrive" Description="MWD Service Provider" LocalCertificateFile="C:\Wanpath\WanPath.Data\Settings\Certificates\mwd.pfx" LocalCertificatePassword="xxxxxxxxxxxxxxxxxx" AssertionConsumerServiceUrl="~/SAML/AssertionConsumerService.aspx"/> </PartnerServiceProviders> <ServiceProvider Name="MyWorkDrive" Description="MWD Service Provider" LocalCertificateFile="C:\Wanpath\WanPath.Data\Settings\Certificates\mwd.pfx" LocalCertificatePassword="xxxxxxxxxxxxxxxxxxxxxxxxx" AssertionConsumerServiceUrl="~/SAML/AssertionConsumerService.aspx"/> <PartnerIdentityProviders> <PartnerIdentityProvider Name="https://iu5.helloid.com/" Description="Manual" PartnerCertificateFile="C:\Wanpath\WanPath.Data\Settings\Certificates\manual.cer" SingleSignOnServiceUrl="https://iu5.helloid.com/relayservice/redirect/ea812515-f34c-465b-a39a-3afb14c15a3c" SignAuthnRequest="true"/> </PartnerIdentityProviders> </SAMLConfiguration>
Import the MyWorkDrive SAML SSL certificate into HelloID
Import the certificate you downloaded from MyWorkDrive. Name it
MyWorkDrive.Go to Applications > Applications and select the Edit link for the MyWorkDrive app.
Select the Configuration tab.
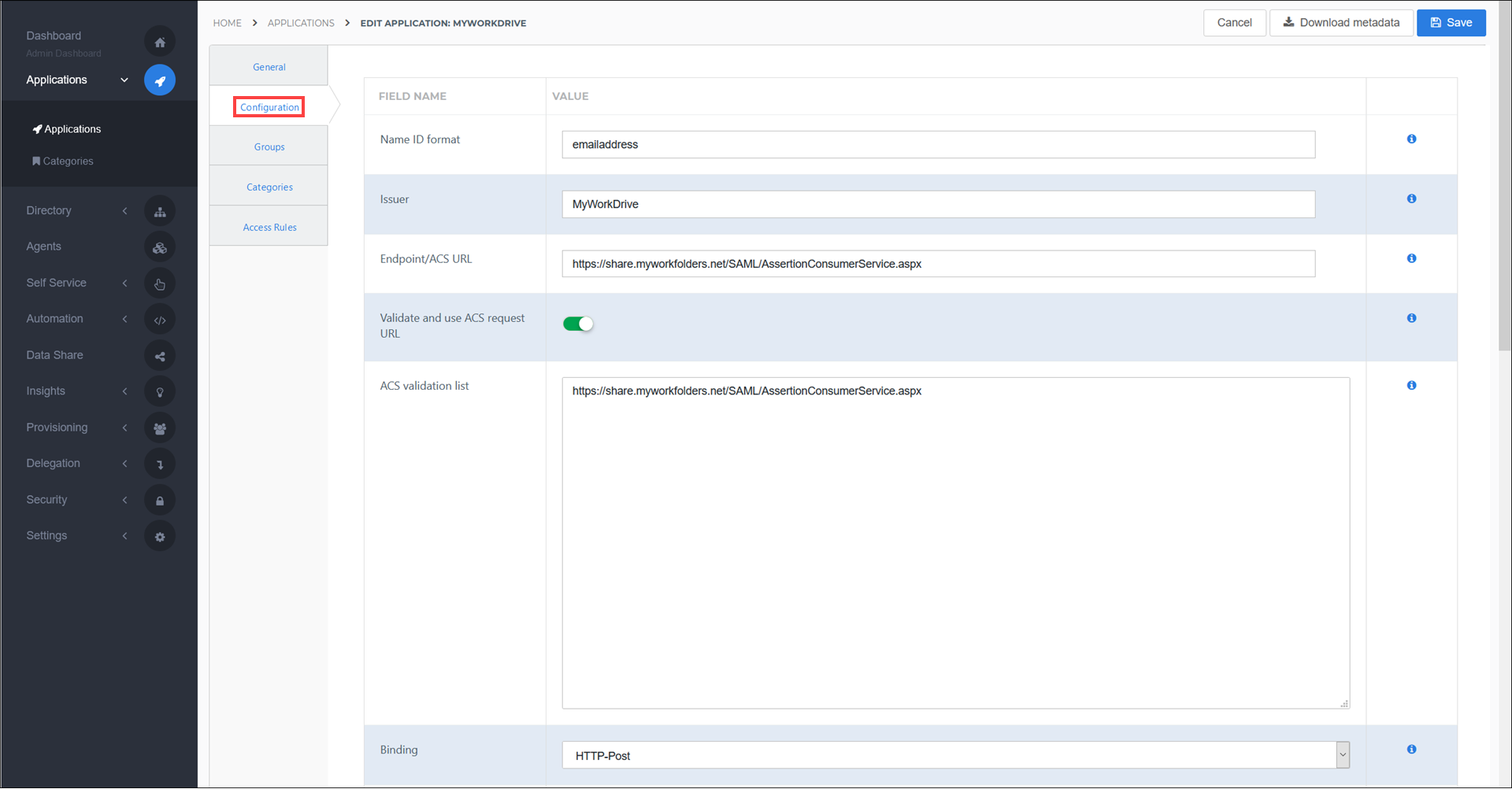
Select the MyWorkDrive certificate in the X509 Encryption Certificate drop down.
Select the Save button.
Finish up
The MyWorkDrive application has been added to HelloID, and a trust has been configured between MyWorkDrive and HelloID. You are now free to assign the application to users within your organization and begin testing it and using it. See Applications - Overview and its related articles for more information.