Nedap Ons OpenID application setup
Introduction
This manual shows how to make an OpenID connection to Nedap Ons. The configuration takes place in HelloID and through a support request to Nedap.
Nedap ONS creates one SSO config for a customer environment.
Nedap ONS works with 1 production system and a number of 'derived' systems. These derived systems form the test systems. This means that all settings are replicated as well. All systems will therefore have the same OpenID Connect data, unfortunately there is no distinction.
This will result in only being able to add 1 SSO application in HelloID, either the test or production environment.
We strongly recommend configuring this for the production environment (and add all other environments as shortcuts).
If the desire is there to include both environments in HelloID, the other environment will have to be a shortcut application in HelloID.
Requirements:
HelloID environment
Nedap Ons environment
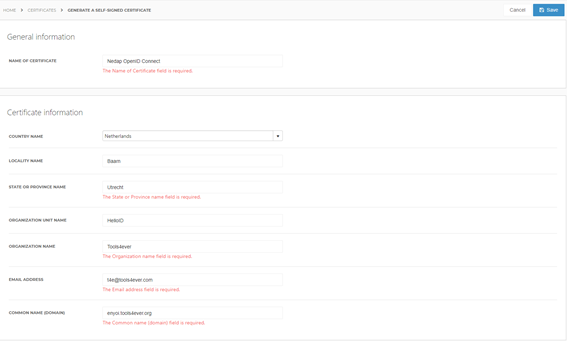
Create or Import a Certificate
If there is no certificate yet, a certificate must be imported or created. This can be done in the HelloID Administrator Portal under Settings > Certificates. For this tutorial, we will use a self-signed certificate. Learn more about certificates here.
Application Setup
Add the Nedap Ons Application
Create a new application in HelloID by navigating to Applications > Applications. Open the Application Catalogue and search for "Nedap Ons". Find the OpenID template, and click Add. Learn more about managing applications here.
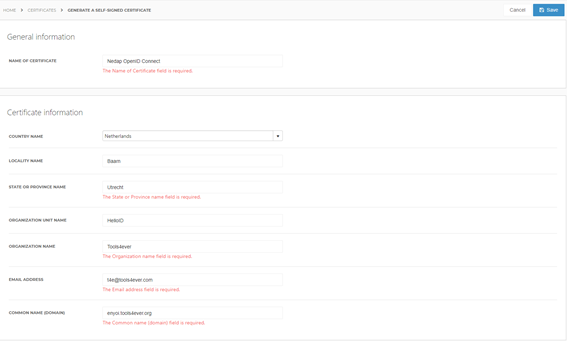
General tab
On the General tab, replace the customer name (klantnaam) in the Default Login URL field. Optionally, you may also add a description. Click Next.
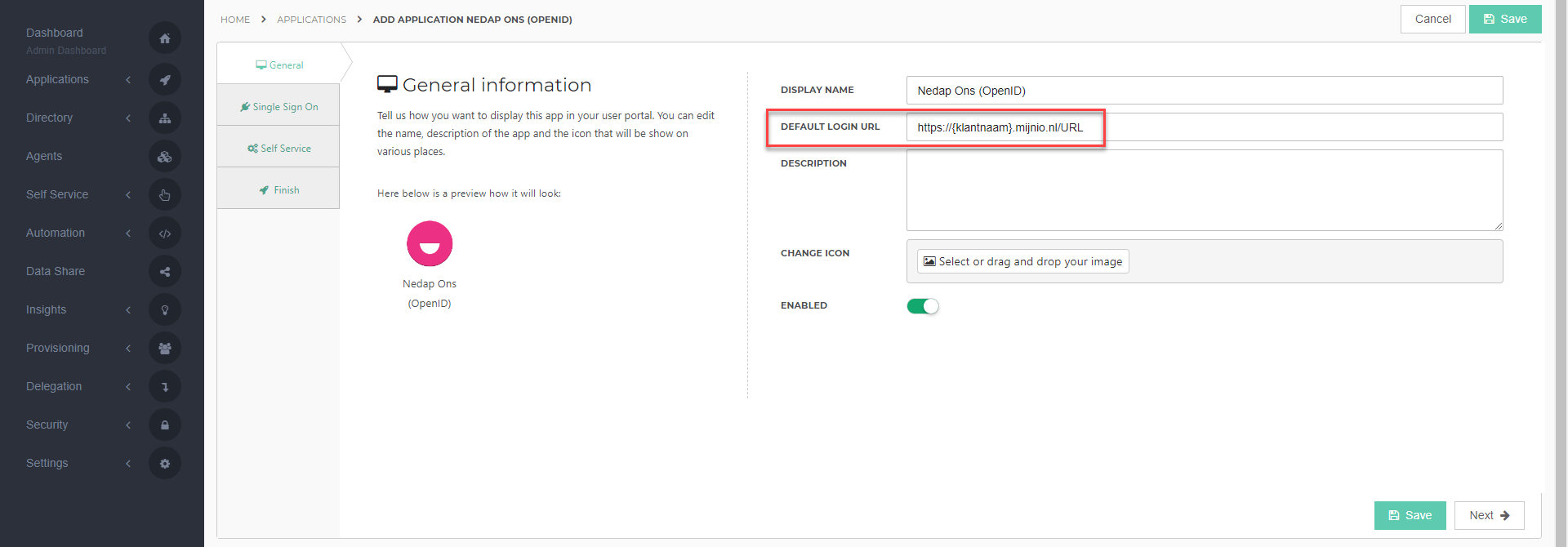
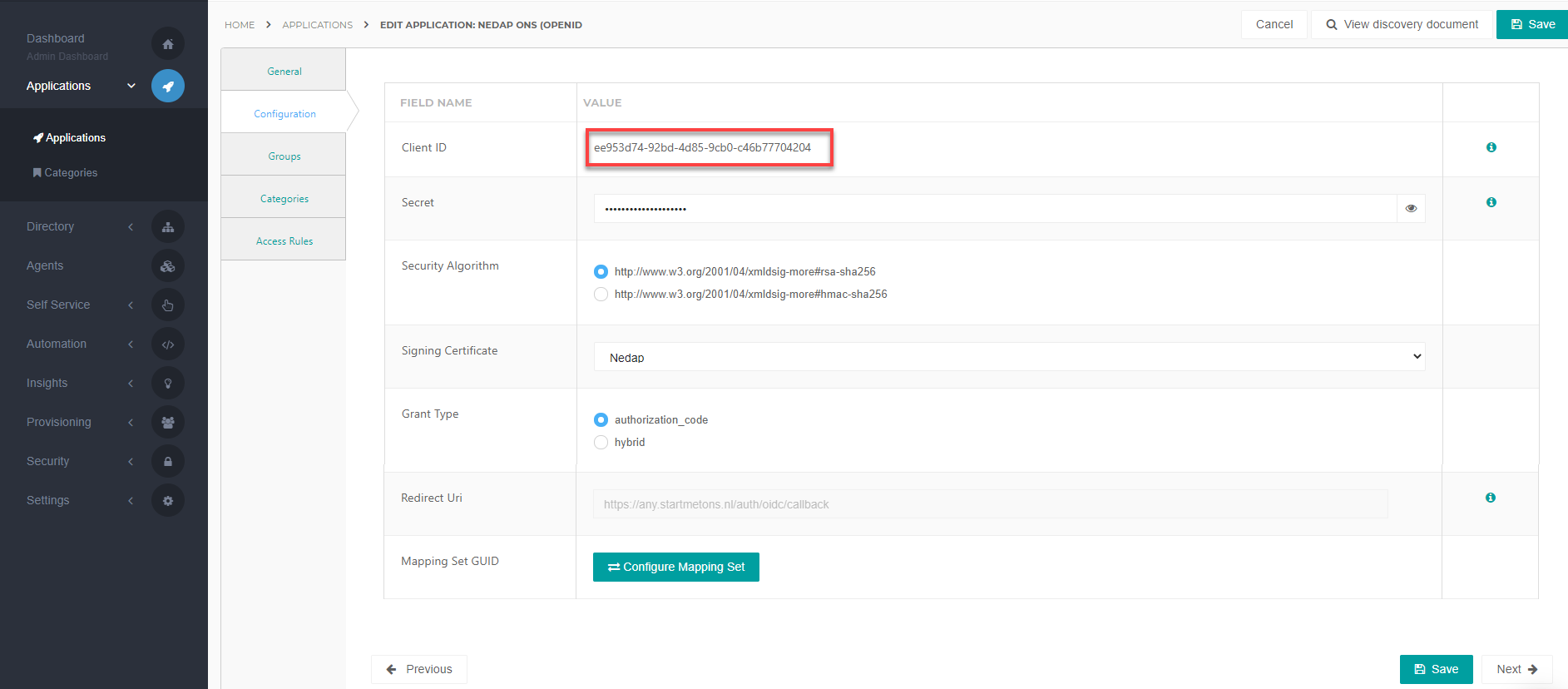
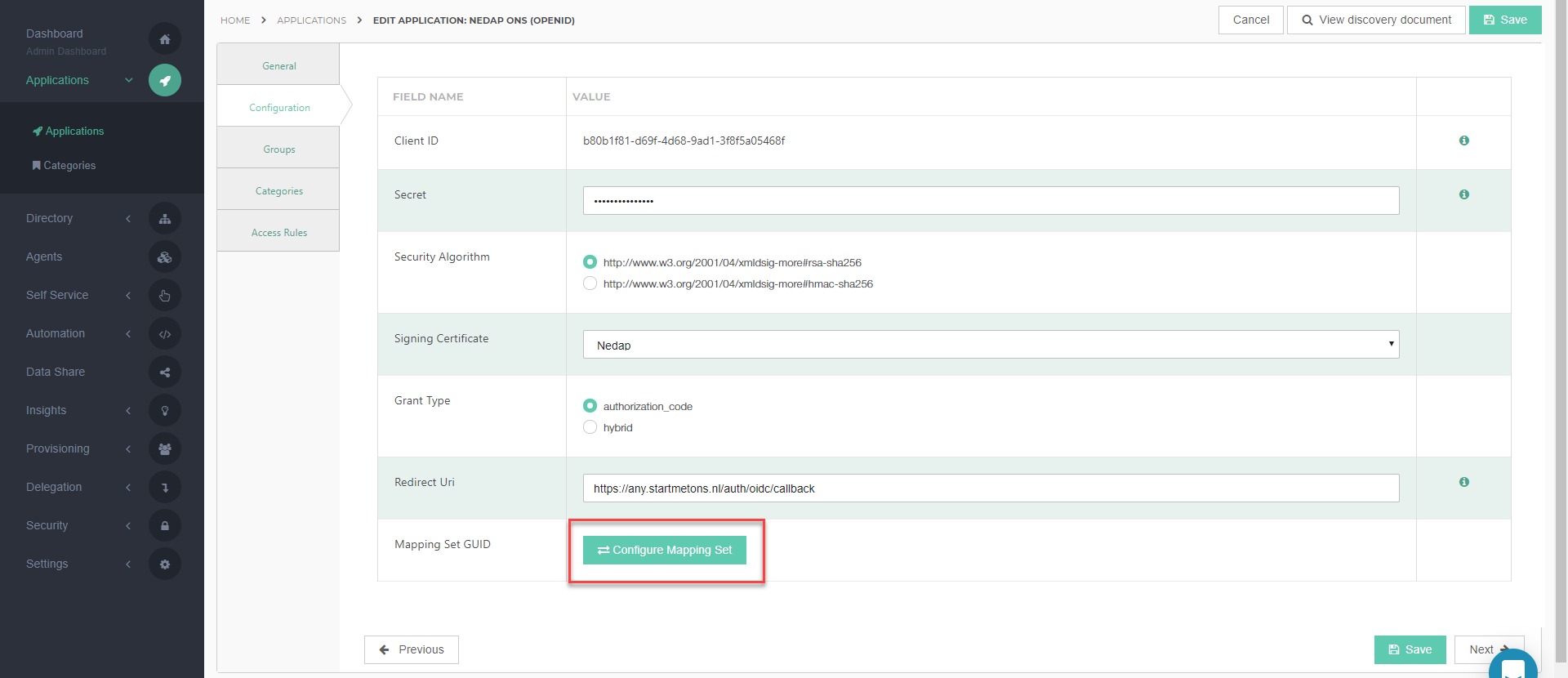
Single Sign-on tab
On the Single Sign-On tab, perform the following steps:
Provide a value in the Secret field. This can be any value that you want. We strongly recommend a value of 52 characters or more. Make note of it, as you will need to supply it to Nedap support later on.
For the Security Algorithm field, select "rsa-sha256", unless otherwise instructed by Nedap support.
In the Signing Certificate dropdown, select the certificate that you created or imported previously.
For Grant Type, verify that "authorization_code" is selected.
At the Redirect Uri, you'll see a pre-provided URL, this is the same for every Nedap environment. Therefore this attribute has a fixed value.
Click Next.
Self service tab
On the Self Service tab, choose whether to automatically create a Self Service product, which makes the application requestable. This is optional. Click Next.
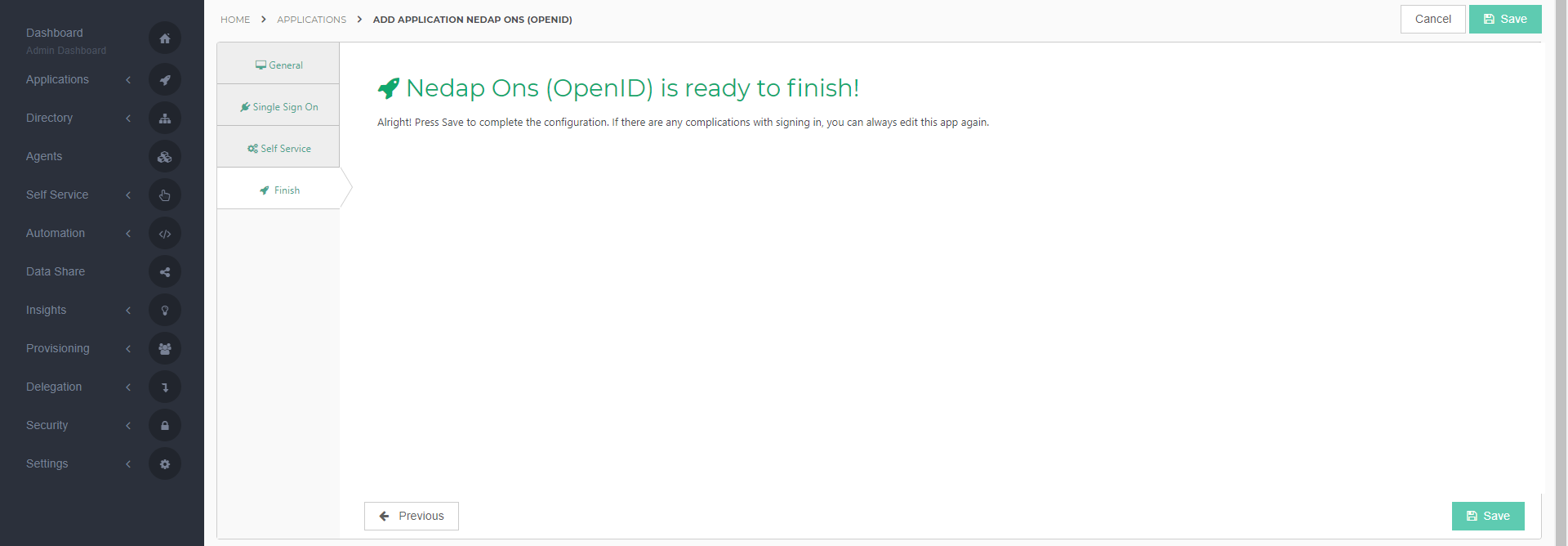
Finish tab
On the Finish tab, click Save to add the application to HelloID.
Additional Configuration
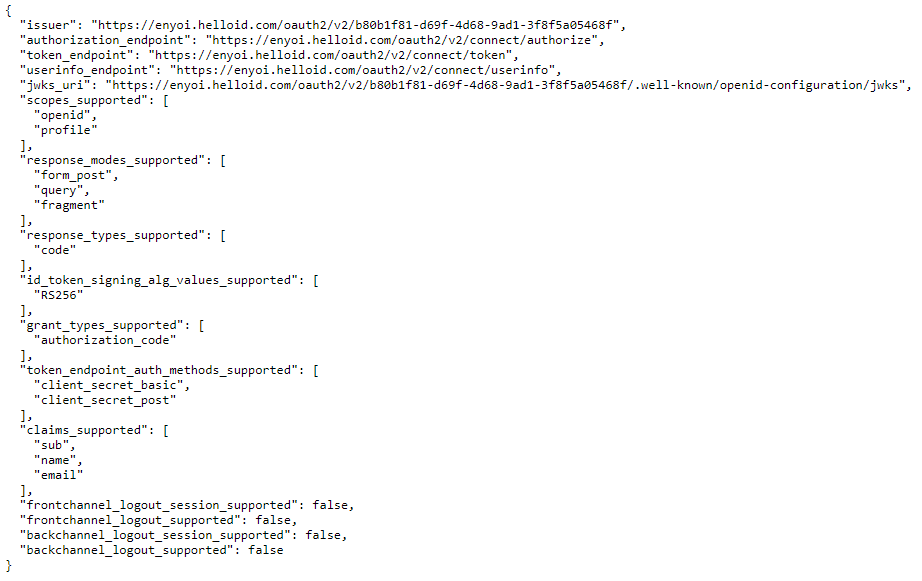
Discovery Document
After adding the Nedap application, click its Edit link on the applications overview. This will bring you to its properties page. Click View discovery document at the right top of the screen.
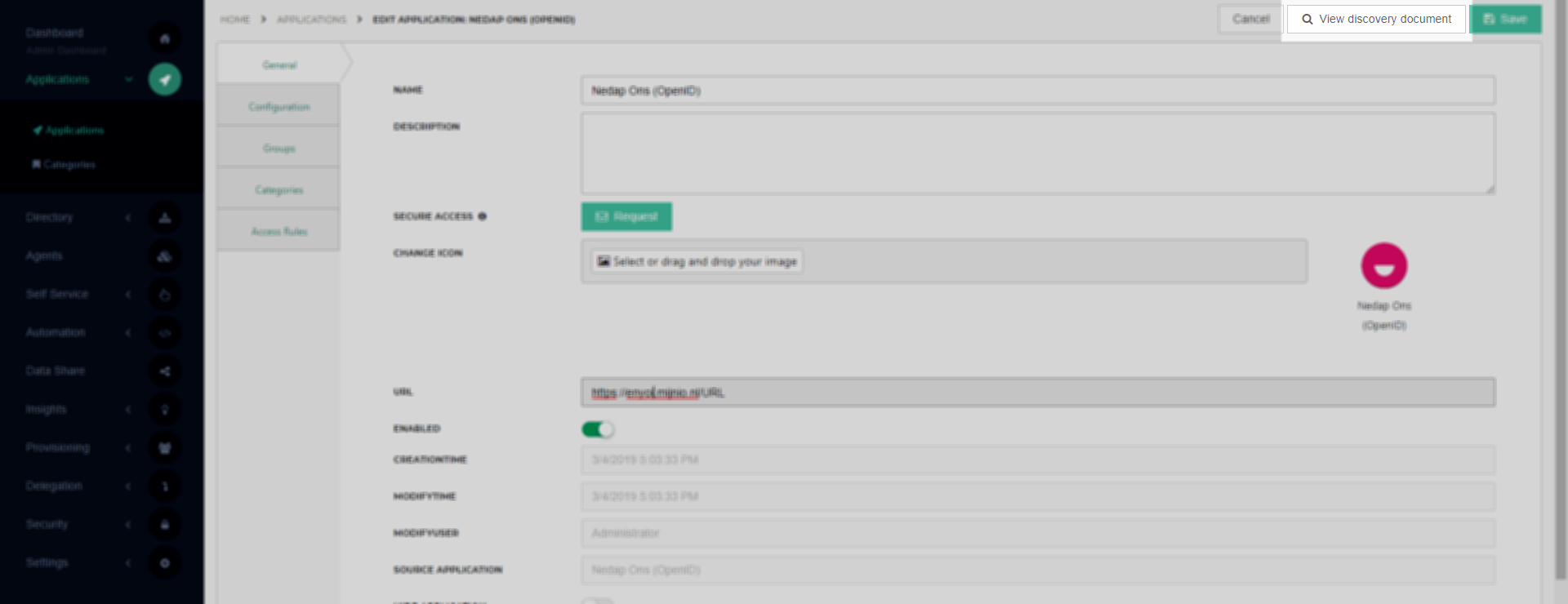
This document contains all the information we will need to send to Nedap. Copy the Discovery Document URL to a program like Notepad for use later on.
Client ID
Back in HelloID, click on the Configuration tab, copy the Client ID to a program like Notepad for use later on.
Configure Mapping Set
After you have copied and stored the Client ID, click Configure Mapping Set. When prompted to leave the page, click Proceed.
Click on the Change Mappings link for the User object. Click the Add mapping link and then provide an additional mapping for the HelloID user's sAMAccountName to the employee_number attribute in Nedap. Your mapping should look like the screenshot below:
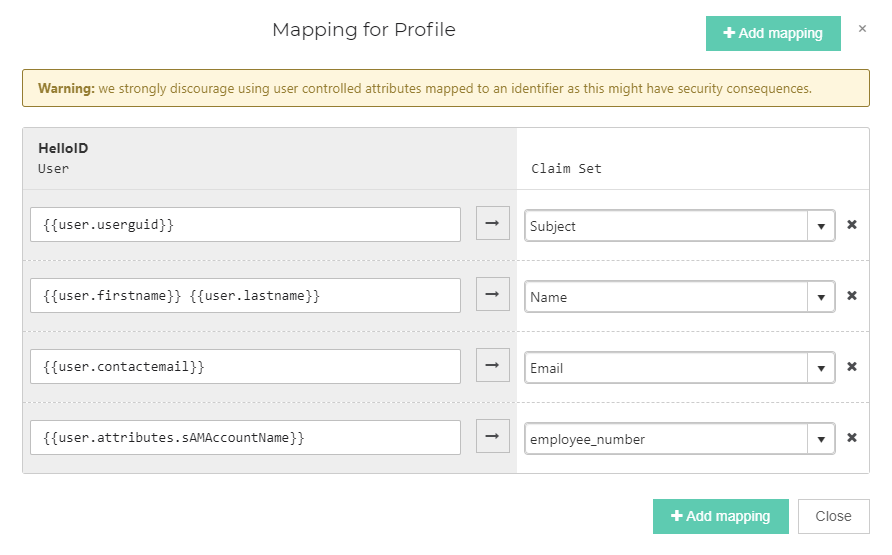
Click Close and then click Save. The configuration of the HelloID application is finished.
Nedap Ons Configuration
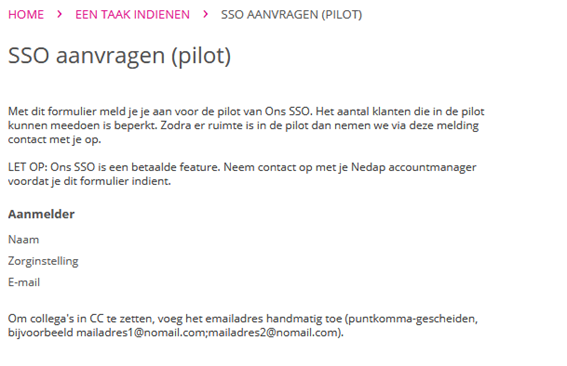
In order to make the connection, Nedap support needs to add the connection on their side. Go to the Nedap TOPdesk portal https://nedap-healthcare.topdesk.net/tas/public/login/form and click the tile SSO AANVRAGEN.
The following information is required:
Name SSO provider: HelloID
Client ID: found at Client ID
Client Secret: created at step 1 at Single Sign-on tab
Issuer: The OpenID Discovery document URL in the format "https://{customer}.helloid.com/oauth2/{application_guid}/.well-known/openid-configuration/"(found at Discovery Document)
Hosted Domain (domain name of the organization, to prevent users from linking a personal account): Your customer domain (example: enyoi.nl)
Text on button (text shown on the button shown at the login screen): To your own liking (something along the lines of "Log in with HelloID")
Button color (Choice between Bright Blue, Dark Blue, Green and Yellow): To your own liking
Hidden? (decides whether the log on button is visible at the login screen): To your own liking
Automatically link users (Would you like to automatically link HelloID users to ONS-users):
Based on e-mail
Based on employee number
Off - no link
Below is an example of the filled out request at Nedap's TOPdesk portal.
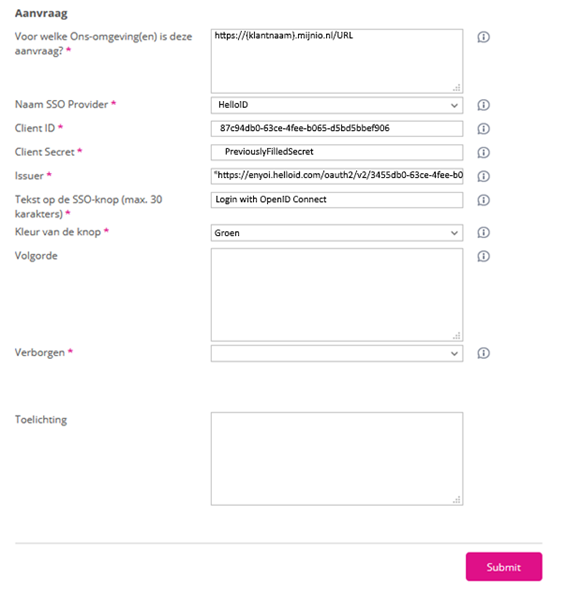
Click Submit and wait for a reaction from Nedap.
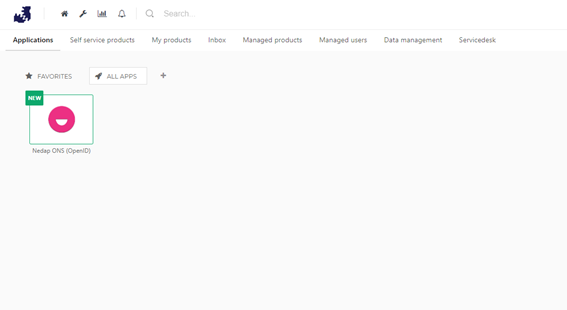
Test the application
After Nedap confirms that the connection has been made on their side, the application is all set for use. It’s time to test the application. Navigate to the HelloID User Dashboard and click on the newly created Nedap application. You should then be authenticated into the Nedap system with no other prompts for credentials.
Nedap ONS Multifactor Authentication Implementation
Step 1: Set up an Identity Provider (IdP)
To use HelloID we advise to setup an identity provider. HelloID can act as an identity provider if none is available. You can use (AD) Active Directory or (AAD) Azure Active Directory as the IdP. This is the used the most, as this is this is commonly available.
Other SAML IdPs are available but may not work out of the box.
To set up Active Directory as your IdP, continue to Step 1a.
To set up Azure Active Directory as your IdP, continue to Step 1b.
1a: Set up Active Directory as your IdP
Your first step is to install the HelloID Agent as described in this article. Next, configure the AD import for the agent as described in this article. Once finished, move on to Step 2 of this article.
1b: Set up Azure Active Directory as your IdP
Follow the instructions in this article to set up and configure Azure AD as your SAML IdP.
Step 2: Set up HelloID Access Policies
Follow the instructions in this article to configure a portal access rule and make sure that multifactor authentication (MFA) is enforced for every login.
Step 3: Set up Nedap ONS
Walk through the steps described here to set up the OpenID connection with Nedap.