Planon SAML application setup
Introduction
This manual shows you how to set up SSO to Planon using the SAML protocol. The configuration takes place in HelloID and Planon.
Requirements:
HelloID environment
Planon environment
Create or Import a Certificate
If there is no certificate yet, a certificate must be imported or created. This can be done in the HelloID Administrator Portal under Settings > Certificates. For this tutorial, we will use a self-signed certificate. Learn more about certificates here.
Application Setup
Add the Planon Application
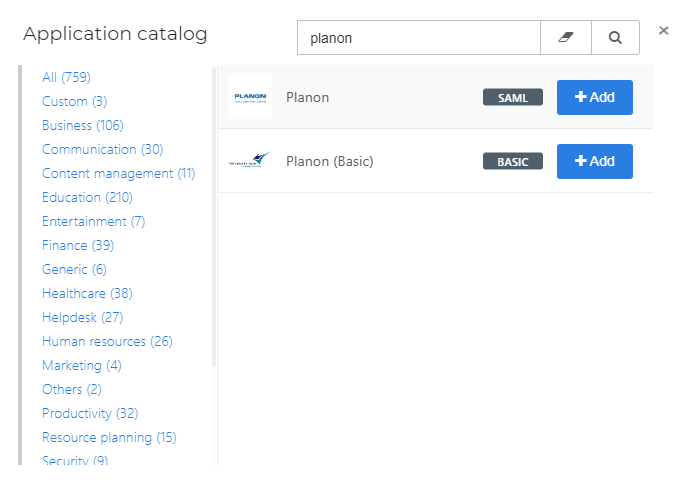
Create a new application in HelloID by navigating to Applications > Applications. Open the Application Catalog and search for "Planon". Find the SAML template, and click Add. Learn more about managing applications here.
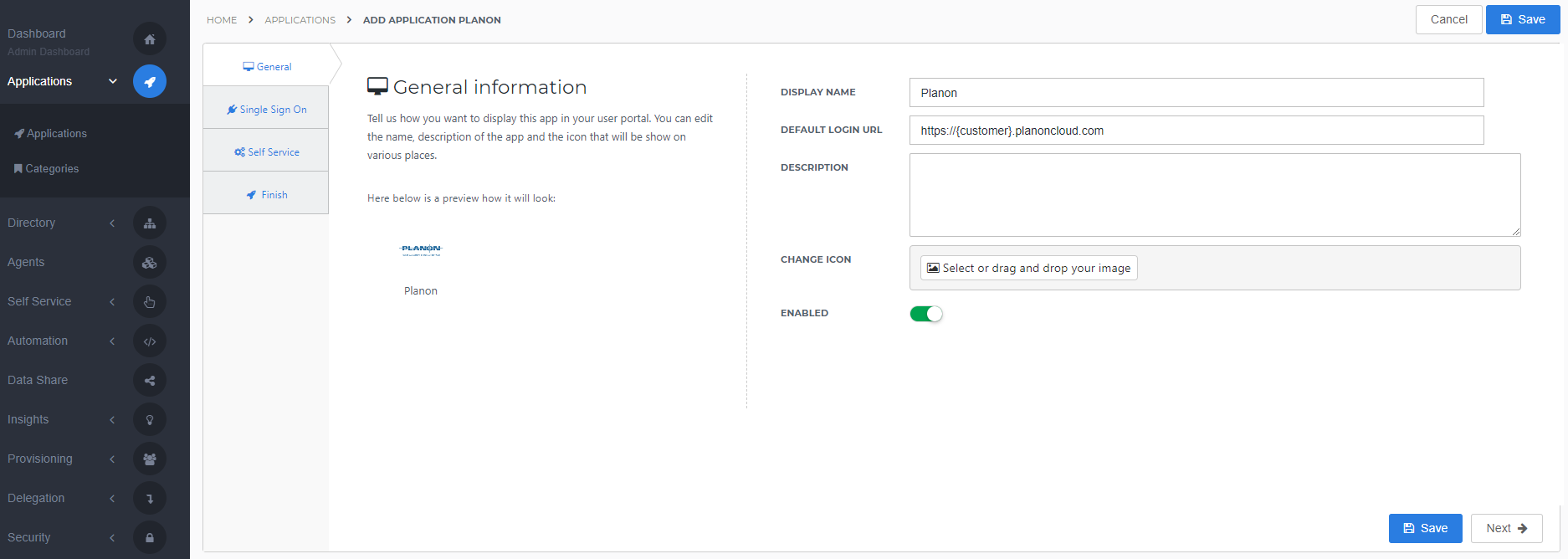
General tab
On the General tab, fill the default login URL with the Planon environment (should be like https://{customer}.planoncloud.com) . Optionally, you may also add a description. Click Next.
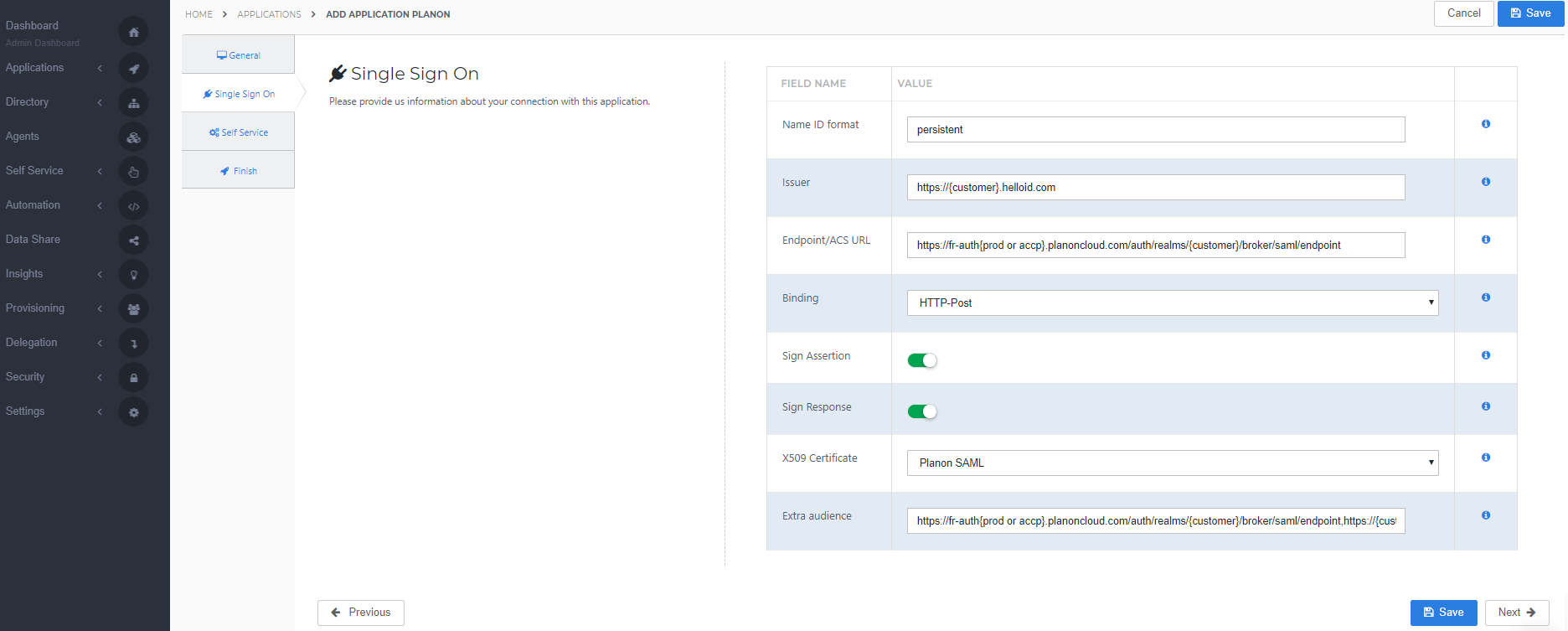
Single Sign-on tab
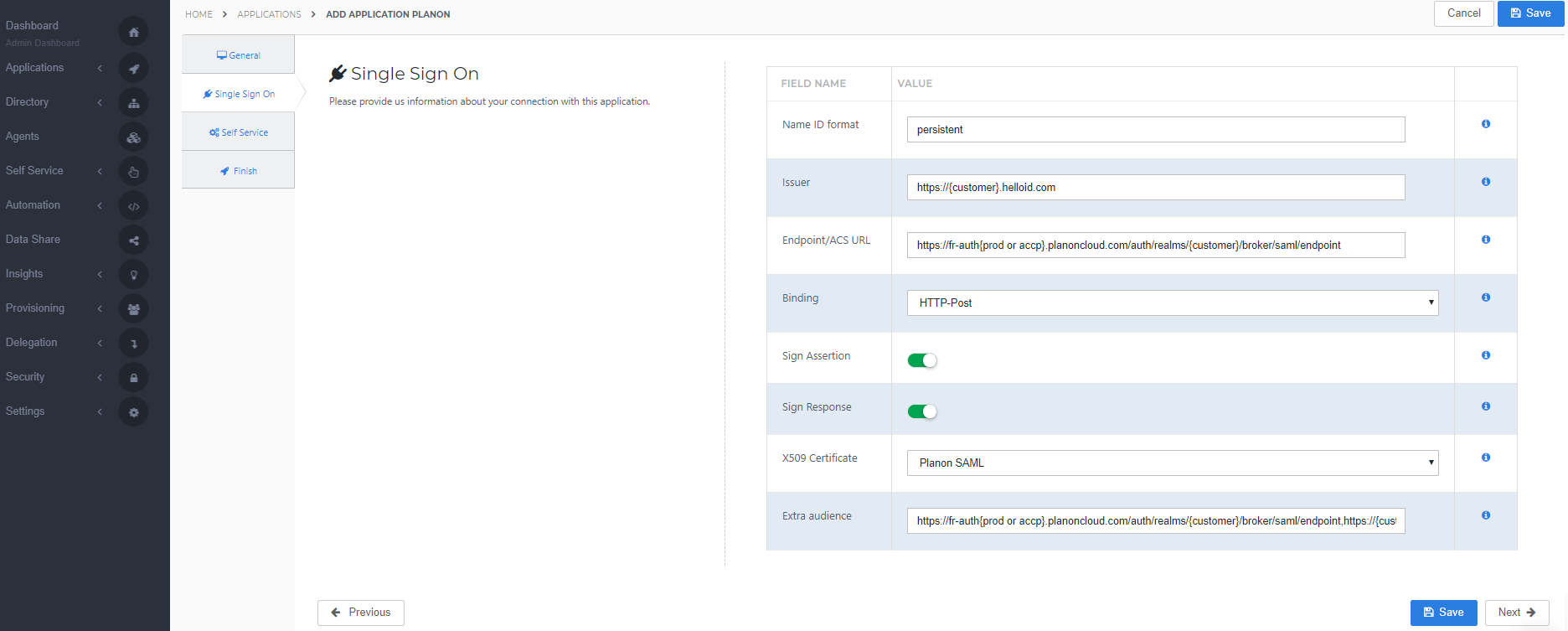
On the Single Sign-On tab, perform the following steps:
Name ID format is by default persistent.
Note: When you change this, it also needs to be changed in Planon
For the Issuer field, provide your HelloID domain in the format "https://{customer}.helloid.com".
Endpoint/ACS URL should be set with the ACS endpoint URL of your Planon environment. This URL is the Redirect URL supplied by Planon or the Planon Administrator. The format should be like
"https://fr-auth{prod or accp}.planoncloud.com/auth/realms/{customer}/broker/saml/endpoint"
Binding is always HTTP-Post (by default).
Sign Assertion is always selected (by default).
Sign Response is always selected (by default).
In the X509 Certificate dropdown, select the certificate that you created or imported previously.
As Extra audience enter the endpoint URL of your Planon environment and your HelloID portal URL in the format "https://fr-auth{prod or accp}.planoncloud.com/auth/realms/{customer}/broker/saml/endpoint,https://{customer.helloid.com}"
Note: (comma separated)
Click Next.
Self service tab
On the Self Service tab, choose whether to automatically create a Self Service product, which makes the application requestable. This is optional. Click Next.
Finish tab
On the Finish tab, click Save to add the application to HelloID.
Configuring the Mapping Set
By default, the 'matching identifier' is set to the user's contact email. This is assuming the email address known in HelloID matches the Planon user's username.
If you wish to use another attribute, click here to learn more about attribute mappings.
Application metadata
After saving the Planon application, click its Edit link on the applications overview. This will bring you to its properties page.
You now have the option to obtain the application metadata.
Dynamic Metadata (URL)
You can simply right-click Download metadata and copy the link address (something along the lines of https://enyoi.helloid.com/metadata/download?ApplicationGUID=e6e741f5-a469-4849-93f7-fe2e259a339f) at the right top of the screen.
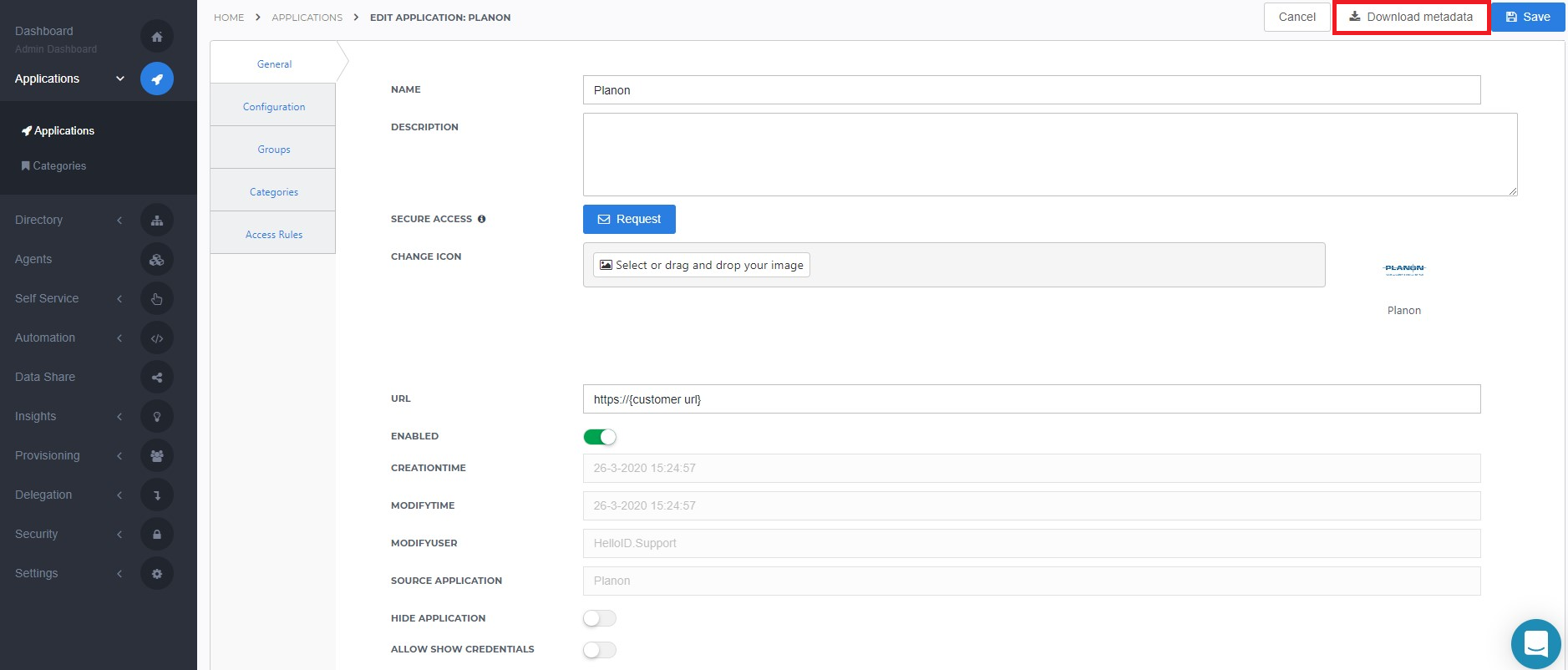
Replace the word 'download' with 'index' in the URL to view the metadata. This URL is the Dynamic Metadata URL.
Please provide this dynamic Metadata URL to Planon or the Planon Administrator.
The configuration of the HelloID application is finished.
Planon Configuration
In order to make the connection, Planon needs to add the connection on their application side. This can be done bij Planon or by the Planon Administrator (superuser) in your organization.
When the Planon Superuser is able to configure the SSO settings in Planon, please follow the steps below.
Sign in to Keycloak and click on Identity Providers
Select the drop-down list Add provider... and select SAML 2.0
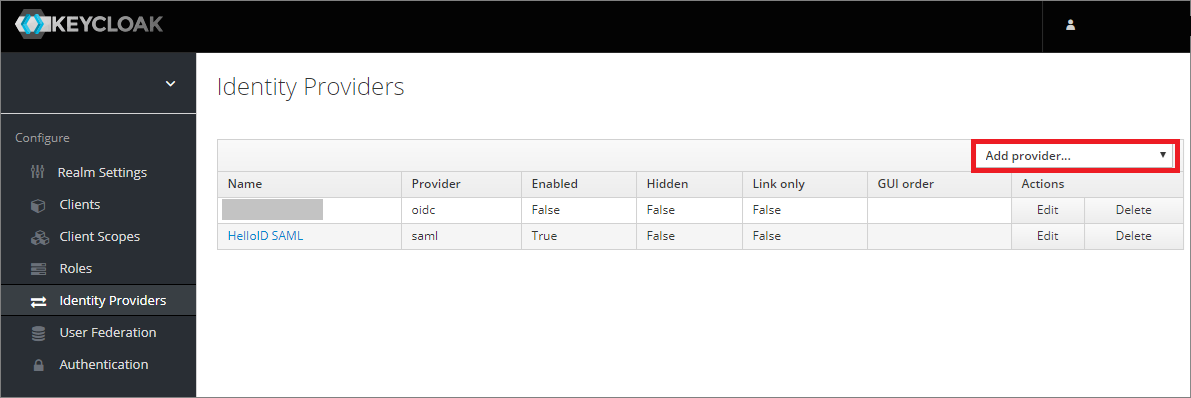
Scroll down to the bottom of the page and paste the Dynamic Metatdata URL and click on Import
The HelloID Metadata will now be imported into the settings of the SAML configuration in Keycloak
Click Save
Finishing Up
The Planon application has now been added to HelloID, and a trust has been configured between Planon and HelloID. You are now free to assign the application to users within your organization and begin testing it and using it. You can learn more about managing applications and assigning permissions here.